Mobile applications have assimilated into our daily life. We primarily rely on these apps to make daily tasks easier, from placing restaurant orders to calling a cab. Testing for mobile application security has grown essential as the use of mobile apps has increased. Mobile applications’ security flaws and vulnerabilities are found using a method called mobile app security testing. To make sure the program is safe from attacks, this procedure entails examining the code, data storage, network connectivity, and user interface.
The significance of mobile application security testing, typical mobile app vulnerabilities, and recommended practices for app security will all be covered in this blog. Also, we’ll highlight some of the best tools for mobile app security testing so you can make sure your app is safe. This blog is a must-read to comprehend the significance of mobile application security testing and how to ensure the security of your app, whether you are a mobile app developer or app owner.
Table of Contents
Get in!
Join our weekly newsletter and stay updated
Why is Mobile Application Security Testing Important?
Mobile application security testing is essential to prevent security breaches, data theft, and other vulnerabilities that could harm users. Here are some reasons why mobile application security testing is important:
- Protecting User Data: Mobile applications store sensitive user data, such as personal information, banking details, and login credentials. Mobile application security testing ensures that this data is secure and not vulnerable to theft.
- Preventing Malware Attacks: Malware attacks can cause significant damage to mobile devices, and it’s essential to prevent them. Mobile application security testing can help identify potential malware attacks and provide a solution to prevent them.
- Maintaining Reputation: A security breach in a mobile application can significantly damage a company’s reputation. Mobile application security testing can help prevent security breaches and ensure the safety of user data, maintaining the company’s reputation.
- Free of Security Risks – Testing the security of a mobile application successfully protects it from threats that can cause data breaches, theft, or loss of sensitive information.
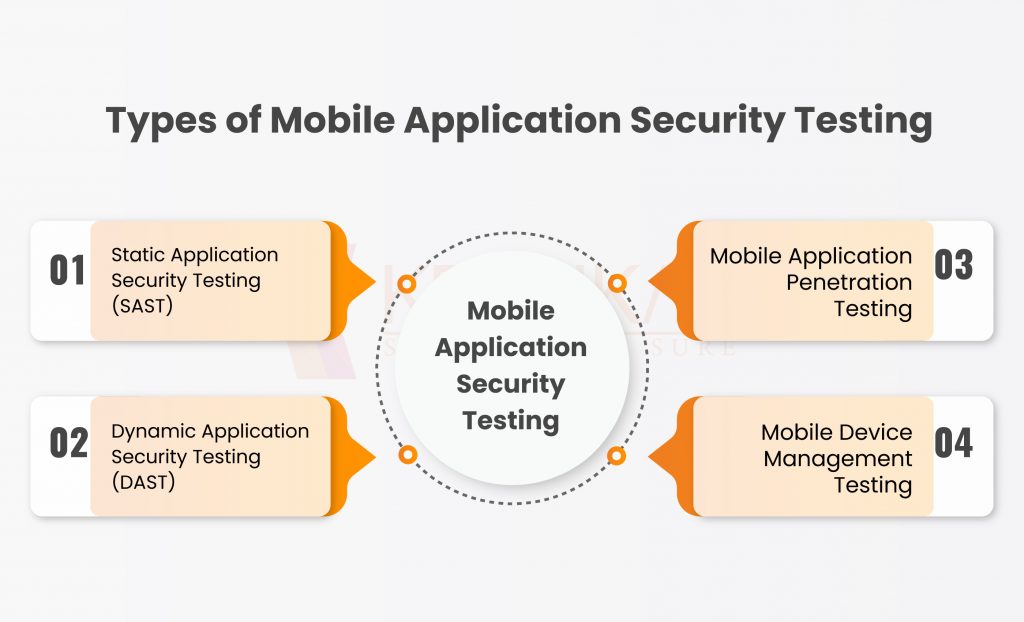
Types of Mobile Application Security Testing:
- Static Application Security Testing (SAST) – Static Application Security Testing is a type of testing that is performed on the source code of the application. It is performed by analyzing the code for potential security vulnerabilities. SAST is a powerful tool for identifying security issues early in the development lifecycle. It helps to reduce the cost of fixing vulnerabilities in later stages of development.
- Dynamic Application Security Testing (DAST) –Dynamic Application Security Testing is a type of testing that is performed on a running application. It is performed by simulating an attack on the application to identify potential vulnerabilities. DAST is a useful tool for identifying vulnerabilities that SAST cannot detect.
- Mobile Application Penetration Testing: Mobile Application Penetration Testing is a type of testing that is performed to identify vulnerabilities in a mobile application. It is performed by simulating an attack on the application to identify vulnerabilities. Penetration testing is a useful tool for identifying vulnerabilities that attackers can exploit.
- Mobile Device Management Testing: Mobile Device Management Testing is a type of testing performed to ensure that the mobile device is secure. It is performed by checking the device configuration, policies, and encryption. MDM testing is a useful tool for ensuring that the device is secure from various threats.
Steps for Mobile Application Security Testing
To find and fix weaknesses in mobile applications, mobile application security testing is crucial. The steps for mobile application security testing are as follows:
- Scope of Testing: Define the scope of testing, including the type of mobile application, the platform on which it will be used, the types of security risks that the application is exposed to, and any regulatory requirements that need to be met.
- Set up the testing environment: Create a testing environment that replicates the real-world scenario as closely as possible, including the mobile devices, operating systems, network configurations, and other necessary tools and software.
- Conduct a threat modeling exercise: Threat modeling is an approach for identifying and evaluating the potential security risks to the mobile application. It helps to identify the potential attack surfaces, entry points, and other security vulnerabilities in the application.
- Vulnerability Assessment to be conducted – A vulnerability assessment involves scanning the mobile application to identify known security vulnerabilities. This can be done using various automated tools that are specifically designed for mobile application security testing.
- Conduct Penetration Testing– Penetration testing is a simulated attack on the mobile application to identify vulnerabilities that may not be found in a vulnerability assessment. This testing is performed manually and requires a skilled tester who can simulate different types of attacks on the mobile application.
- Analyze the results-It is important to assess and interpret the test results after they have been completed. In order to prioritize them for remediation, it is necessary to analyze the vulnerabilities that have been found and determine their severity and impact.
- Fix the vulnerabilities: The mobile application’s vulnerabilities need to be corrected in light of the testing’s findings. This could entail setting up the network, updating the application code, or altering the settings on the mobile device.
- Re-test the application: Once the vulnerabilities have been fixed, the mobile application should be re-tested to ensure that the vulnerabilities have been remediated and that the application is secure.
- Document the results: The findings of the testing should be recorded in a report, along with the vulnerabilities found, their severity, the corrective actions performed, and any recommendations for future security testing.
Get in!
Join our weekly newsletter and stay updated
Securing your Application
The mobile application security testing services offered by Kratikal, a cert-in empanelled organization seem to provide a full range of options to support businesses in ensuring the security of their mobile applications. They offer manual and automated testing services that address many different types of vulnerabilities, such as problems with login and authorization, data leaks, and malware attacks.
Static and dynamic analysis techniques are combined as part of Kratikal’s testing methodology, which might aid in locating vulnerabilities that different testing methods would miss. In-depth reports are also delivered, highlighting any vulnerabilities discovered and offering suggestions for how to fix them.
Overall, it appears that organizations trying to secure the security of their mobile applications may find Kratikal’s services to be a helpful resource. To guarantee that their services are in line with your organization’s unique security requirements, as with any security testing service, it’s crucial to carefully assess the provider’s skills.









Leave a comment
Your email address will not be published. Required fields are marked *