In the digital age, businesses are reliant on the Internet for their operations, from communication and data storage to e-commerce and customer engagement. The digital transformation has ushered in benefits but also introduced new threats. DDoS cyber attacks stand out as being particularly widespread and unfavorable among them.
In this blog, we will explain why every business, regardless of size or sector, must contend with the threat of DDoS attacks.
Table of Contents
Introduction to DDoS Cyber Attacks
A distributed denial of service (DDoS) attack is a malicious attempt to stop a community, service provider, or website from operating normally by saturating it with an excessive amount of internet traffic. This onslaught of website traffic is produced by a jumble of hacked machines, frequently constituting a botnet, which floods the target with website visitors until it becomes gradually unavailable. A DDoS attack aims to make the target service unavailable to its users, causing inconvenience, monetary losses, and reputational damage.
The Threats from Opensource DDoS Tools
Open-source DDoS tools pose a significant and ever-evolving threat to online security. These tools, often developed and shared freely in the digital underground, empower malicious actors with the means to orchestrate devastating Distributed Denial of Service attacks. These tools have been instrumental in the hands of ethical hackers and security researchers for testing network resilience, their availability to malicious entities cannot be overlooked.
Cyber attackers leverage open-source DDoS tools to create large-scale, distributed attacks that can paralyze websites, services, and online infrastructure. As a result, organizations of all sizes must remain vigilant, implement robust security measures, and stay informed about emerging threats to mitigate the risks posed by these readily accessible and adaptable tools.
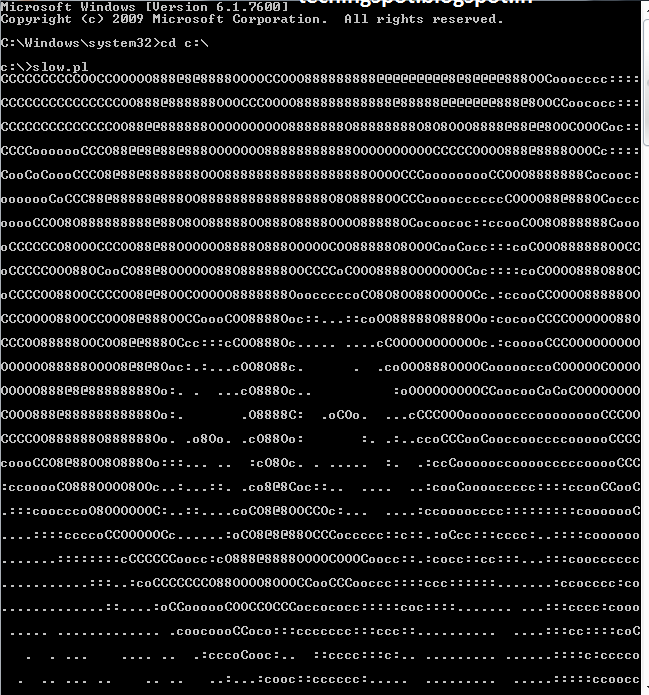
One such example is the “Slowloris” tool, which operates by launching stealthy and keeping alive packets on a target server by initiating a multitude of partial connections, keeping them open indefinitely.
What makes open-source DDoS tools particularly risky is their accessibility and adaptability. These tools are accessible to anyone who has an understanding of technology, who may then alter them and use them against weak targets. Organizations must be attentive and proactively strengthen their defenses as the threat landscape changes to prevent attacks from open-source DDoS tools and other related threats.
Why DDoS Cyber Attacks Pose a Threat to Every Business?
It is generally seen that DDoS cyber attacks primarily target commercial companies, regardless of the intentions behind these attacks. As long as they keep an online presence, even small enterprises and major corporations are vulnerable to these attacks. Several important characteristics highlight the seriousness of the threat that DDoS cyber attacks pose to businesses:
Neglection of DDoS Prevention and Security
Traditional approaches no longer work in the new environment of highly sophisticated attacks, and even rapid attacks can cause significant financial and reputational loss.
While attacks on larger firms often make headlines, SMEs should not assume they are immune. Unfortunately, this misconception can lead SMEs to underestimate the importance of DDoS mitigation, making them attractive targets for attackers.
Widening Scope of Vulnerability
The widespread use of Bring Your Device (BYOD) on potentially insecure networks has surged. Consequently, every organization faces an expanded attack surface and heightened susceptibility to DDoS threats. The situation worsens when organizations fail to grasp the significance of DDoS protection and rely on off-the-shelf or default solutions offered by hosting ISPs, or cloud service providers
Disruption of Services
DDoS attacks aim to flood a target’s network or website with a massive volume of traffic, overwhelming their infrastructure. This results in services becoming slow or completely unavailable to legitimate users. For businesses reliant on online operations, any disruption can lead to financial losses and damage to their reputation.
Financial Losses
DDoS cyber attacks can have severe financial consequences. Businesses may lose revenue during the attack due to the inability to process transactions, and there can be additional costs associated with mitigating the attack, such as investing in DDoS protection services or hardware.
Data Breach Risk
DDoS cyberattacks might be used as a distraction strategy. Hackers may take advantage of vulnerabilities to get unauthorized access to critical information, resulting in data breaches, while a company is occupied defending against a DDoS attack.
Get in!
Join our weekly newsletter and stay updated
How to Protect Business from DDoS Cyber Attacks?
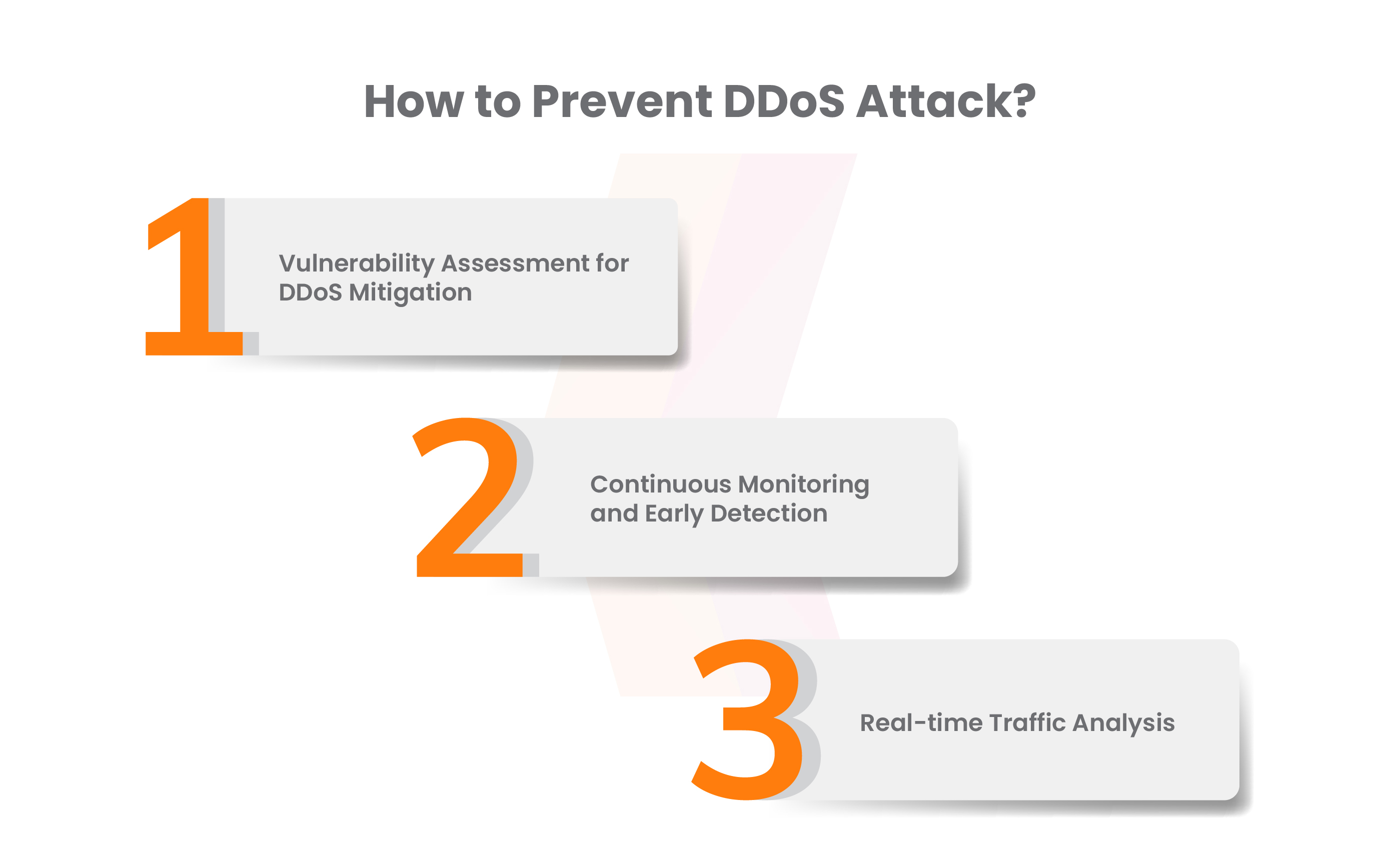
Vulnerability Assessment for DDoS Mitigation
VAPT (Penetration) services can conduct comprehensive vulnerability assessments to identify weaknesses in your network infrastructure that might be exploited in a DDoS attack. By addressing these vulnerabilities, you can reduce the risk of successful DDoS cyber attacks.
Continuous Monitoring and Early Detection
VAPT services often include continuous monitoring capabilities. By leveraging VAPT tools and expertise, you can detect early signs of an impending DDoS attack. This proactive monitoring allows you to take immediate action and minimize the impact of an attack before it disrupts your services.
Real-Time Traffic Analysis
Implement real-time traffic analysis tools as part of your VAPT services. These tools can continuously monitor incoming traffic for anomalies and patterns associated with DDoS attacks. When unusual traffic is detected, automatic mitigation measures can be initiated to protect your network.
Significance of DDoS Protection
The significance of DDoS (Distributed Denial of Service) safety cannot be emphasized in a virtual world that is becoming more linked. In order to protect against those disruptive cyber attacks, organizations of all sizes and sectors must take the following precautions:
Accessibility of Website
One of the most immediate consequences of a DDoS cyber attack is the inundation of a website with an excessive volume of requests, depleting its resources and rendering it inaccessible to genuine traffic. Throughout the attack’s duration, any business interactions conducted through the website become unavailable, causing harm to both the brand’s image and its reputation.
However, by implementing efficient DDoS protection measures, businesses can guarantee the continuous availability of their website and digital assets. These protective measures encompass globally distributed content delivery networks (CDNs) designed to enhance website speed and performance while maintaining robust security measures.
Ensure Website Security from different cyber attacks
DDoS cyber attacks are often deployed as diversions to mask other cyberattacks, including malware infiltration, establishment of backdoors, account hijacking, extortion, and data scraping, among others. By employing comprehensive, all-encompassing DDoS services, you can maintain continuous surveillance over incoming traffic, proactively address vulnerabilities before malefactors exploit them, and safeguard your digital assets comprehensively.
Save Capital, Time, and Other Resources
DDoS attacks, much like other forms of cyber threats, can inflict significant financial and reputational harm. Employing managed and user-friendly DDoS prevention services to shield websites translates into substantial savings in terms of time, financial resources, and effort.
Book Your Free Cybersecurity Consultation Today!
Conclusion
DDoS attacks represent a threat that every business must take seriously. The constant threat posed by these cyberattacks is a result of the Internet’s interconnectedness, the development of Internet of Things (IoT) devices, easily available attack tools, developing attack strategies, and financial reasons. Businesses must commit to enhancing their security posture if they want to effectively manage this risk. This entails making investments in effective defenses like DDoS mitigation programs, putting policies in place for employee training, and creating clearly defined incident response plans. Companies can lessen their susceptibility to DDoS attacks, protecting their digital operations and maintaining their reputation in the digital realm, by proactively recognizing possible risks and putting in place thorough protection measures.
Regular VAPT testing and sufficient security compliance can help organizations stop such threats. With an emphasis on securing web applications from potential threats, Kratikal provides complete cybersecurity solutions built to protect enterprises from a variety of cyberattacks. As a CERT-In-Empanelled company, Kratikal assists organizations in identifying and repairing security flaws before hackers can use them against them.









Leave a comment
Your email address will not be published. Required fields are marked *