Protecting your digital assets has become a top priority due to society’s growing reliance on technology. Protecting sensitive data, preventing data breaches, and preserving the privacy and integrity of digital assets all depend on cybersecurity. Organizations and people must both develop solid frameworks that offer a complete approach to cybersecurity if they are to effectively protect against cyber threats.
Modern corporate operations must take cybersecurity seriously, and with the threat landscape continually changing, it’s more critical than ever to remain on top of things. A multi-layered strategy, including the installation of efficient security measures and the adoption of industry-standard frameworks, is needed to protect digital assets, such as sensitive data and information. The top cybersecurity frameworks of 2023 will be discussed in more detail in this blog post, along with how you can use them to safeguard your data and preserve your digital assets.
Table of Content
Security Framework
A company should adhere to a cyber security framework, which is a collection of best practices, to manage the risks related to cybersecurity. This security framework’s primary objective is to identify the business environments that offer a high risk for data breaches and to establish rules, procedures, and controls to lower those risks to manageable levels.
These security frameworks frequently offer a set of instructions for creating a solid security posture and safeguarding digital assets and sensitive data from online attacks.
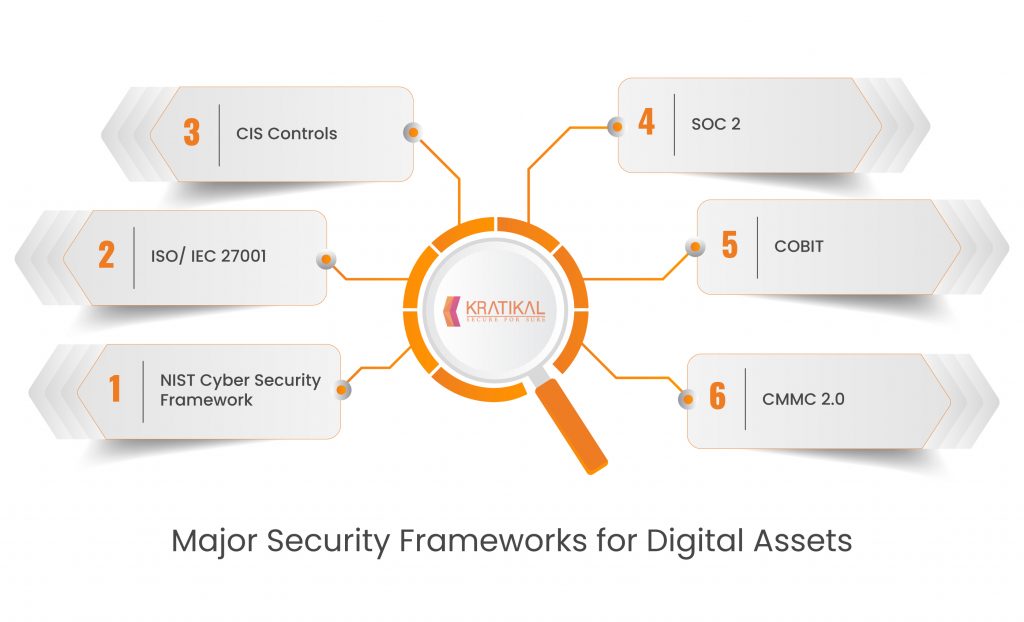
Major Security Frameworks for Digital Assets
Let’s examine the main security framework for protecting digital assets in further detail and how it can guarantee the security of your data.
- NIST Cyber Security Framework
- ISO/ IEC 27001
- CIS Controls
- SOC 2
- COBIT
- CMMC 2.0
Many technologies, frameworks, and best practices are available under the heading of information security. The main frameworks for protecting digital assets will be thoroughly explained.
- NIST Cyber Security Framework – The National Institute of Standards and Technology (NIST) developed the NIST Cybersecurity Framework, a management and risk-reduction framework for cybersecurity. With an emphasis on the five fundamental cybersecurity functions of Identity, Protect, Detect, React, and Recover, it offers a risk-based approach to cybersecurity. The framework has a strong emphasis on continuous development and provides organizations with guidelines, best practices, and assessment tools to help them create efficient cybersecurity policies and procedures. The Identify function prioritizes assets, systems, and data that need to be protected in order to understand and manage cybersecurity risks. In order to defend against cybersecurity threats, the Protect function implements protections and procedures like access limits, encryption, and employee awareness training. The Detect function continuously monitors and analyzes systems and networks with the goal of quickly identifying cybersecurity occurrences. For the purpose of managing and mitigating cybersecurity incidents, the Respond function develops and implements reaction strategies. After a cybersecurity incident, the Recover function aims to get things back to normal by restoring backups and applying lessons learned.
- ISO/ IEC 27001 – A widely accepted international standard for information security management systems is ISO/IEC 27001. (ISMS). It offers businesses a thorough framework for developing, implementing, maintaining, and continuously enhancing an ISMS, which is a methodical strategy for managing and safeguarding sensitive information. Organizations must carry out risk analyses and put controls in place to reduce identified risks in accordance with ISO/IEC 27001. It also underlines the significance of a management-driven strategy for information security, including a commitment from the top down, risk management, and ongoing development. The accomplishment of ISO/IEC 27001 accreditation shows a company’s dedication to information security best practices and can strengthen its cybersecurity position.
- CIS Controls – The Center for Internet Security (CIS) Controls are a list of actions with priority rankings that offer detailed advice for enhancing a company’s cybersecurity posture. The CIS Controls are divided into three groups: Organizational, Foundational, and Basic. The Basic Controls are focused on implementing fundamental cybersecurity measures, such as secure device configuration, continual vulnerability assessment and remediation, and inventory and management of hardware and software assets. The Foundational Controls are designed to improve an organization’s defenses by putting in place procedures like multi-factor authentication, data recovery, and security awareness training. The organizational controls, which include creating an incident response strategy, performing security audits, and guaranteeing third-party security, are centered on enhancing an organization’s cybersecurity governance and risk management.
- SOC 2 – The American Institute of Certified Public Accountants (AICPA) developed the System and Organization Controls (SOC) 2 framework as a set of guidelines for evaluating the security, availability, processing integrity, confidentiality, and privacy of data in service organizations. Organizations frequently utilize SOC 2 to evaluate the security and privacy safeguards of their service providers. Customers and stakeholders can have confidence that an organization’s controls are set up and working efficiently to secure their data and comply with SOC 2 requirements thanks to SOC 2 reports that independent auditors publish.
- COBIT – A leading framework for IT governance and management was created by ISACA and is called COBIT (Control Objectives for Information and Associated Technologies) (Information Systems Audit and Control Association). It offers a thorough set of standards and best practices for overseeing and managing information technology in businesses with a focus on coordinating IT with corporate objectives, guaranteeing risk management, and getting the most out of IT expenditures.
Conclusion
To protect your digital assets, you can utilize a variety of frameworks. Your digital assets’ particular needs and requirements, as well as the level of security you want to attain, will determine the optimal framework. As a result, a thorough strategy that incorporates multi-factor authentication, encryption, frequent updates and patches, access controls, incident response planning, employee awareness and training, and regular security audits and assessments can offer a solid framework to protect your digital assets from a variety of cyber threats.
To keep up with changing threats and effectively safeguard your digital assets, it is crucial to regularly review and upgrade your security procedures.
Kratikal, a CERT-In empanelled organization can assist businesses in defending themselves against a variety of cyberattacks and protecting digital assets. Web and mobile application security, network and cloud security, and compliance and risk management are among the services and products the business provides. Before attackers may take advantage of vulnerabilities in systems and apps, Kratikal assists enterprises in identifying and fixing those issues.
With a focus on providing individualized and affordable solutions, Kratikal can assist businesses of all sizes and in a variety of sectors to strengthen their cybersecurity posture and safeguard their priceless information and assets.