Every firewall in the market is vulnerable to hacking, despite what certain security providers may assert. Threat actors can still defeat a firewall’s security measures by employing a number of strategies.As cybersecurity becomes increasingly important in today’s digital age, it’s crucial to understand how to protect your system from potential threats.
One key aspect of cybersecurity is the use of a firewall, which acts as a barrier between your network and the outside world. However, even the most advanced firewall can be breached if not properly configured or maintained.
Firewalls are an essential tool for protecting your network and devices from external threats. They act as a first line of defense against cyber attacks and prevent unauthorized access to your sensitive data. However, even with a firewall in place, there is still a risk of it being breached.
In this blog, we’ll delve into the top 5 ways a firewall can get breached, so you can take the necessary steps to prevent it from happening to your system.
Table of Contents
Get in!
Join our weekly newsletter and stay updated
How does Firewall work?
A firewall is a security system that monitors and controls incoming and outgoing network traffic based on predetermined security rules. It is used to protect a network or device from unauthorized access or attacks.
Firewalls can be hardware-based, software-based, or a combination of both. They are often used to protect a network from external threats such as malware, viruses, and hackers. Firewalls can also be configured to allow or block specific types of network traffic based on various criteria such as IP address, port number, and protocol.
It’s crucial to first comprehend how a firewall operates before attempting to hack one. A firewall keeps track of all network traffic, both inbound and outbound, and, depending on the rules that have been set up, either permits or prohibits that traffic from getting to its destination. The fact that firewalls are frequently the initial line of defense in a network makes them an example of perimeter security.
Techniques Employed by Firewalls
At least one of the following techniques is employed by firewalls to keep track of network traffic:
- Packet Filtering – The majority of firewalls are of this kind. Small pieces of data called packets are examined by a number of filters as they try to enter the network. Afterward, based on the source and destination of IP addresses, protocols, and ports, the firewall decides whether or not they are permitted to enter.
- Application/Gateway Firewall – By filtering traffic at the application level, this technique. In order to prevent direct connections between the device and incoming packets, proxy servers operate as middlemen.
- Next-generation Firewall (NGFW)- To defend against both web-based and network assaults, these sophisticated firewalls integrate classic network firewall technologies with web application firewalls (WAFs). An NGFW also includes additional features including antivirus, encrypted traffic inspection, and intrusion prevention systems (IPS). Deep packet inspection, which examines the data in the packet payload rather than simply the packet header, is one characteristic of an NGFW.
- Stateful Inspection – This is a more recent technique that examines the packet for particular distinguishing traits while comparing important packet components to a database. The packet is permitted to pass if there is a reasonable match.
“Don’t let your firewall become a weak link in your cybersecurity strategy.”
Methods of Evasion
Despite the fact that Firewalls and IDS can stop malicious packets from entering a network, an attacker can send altered packets to the target in order for it to get past the IDS/Firewall. These evasion methods come in a variety –
- Encrypting data: By encrypting the data being transmitted, it becomes more difficult for the firewall or intrusion detection system to detect any malicious activity.
- VPN: A virtual private network (VPN) can help bypass firewalls and intrusion detection systems by routing traffic through a secure server.
- Proxy server: A proxy server can help mask the origin of the traffic, making it harder for the firewall or intrusion detection system to trace the source of an attack.
- TOR: The TOR network can help hide the identity of the user and the origin of the traffic, making it harder for the firewall or intrusion detection system to detect any malicious activity.
- Port hopping: By constantly changing the port used to transmit data, it becomes more difficult for the firewall or intrusion detection system to detect any malicious activity.
- Steganography: By hiding data within another file or message, it becomes harder for the firewall or intrusion detection system to detect any malicious activity.
- Application layer protocols: By using application layer protocols such as HTTP or SMTP, it becomes harder for the firewall or intrusion detection system to detect any malicious activity.
- Malicious code: By using malicious code or malware, it becomes harder for the firewall or intrusion detection system to detect any malicious activity.
- Social engineering: By tricking users into divulging sensitive information or taking certain actions, it becomes easier for an attacker to bypass the firewall or intrusion detection system.
- Physical access: By physically accessing the network or system, an attacker can bypass the firewall or intrusion detection system.
Ways a Firewall can get Breached
A firewall is a crucial security feature that helps to protect your computer or network from external threats such as hackers and malware. However, despite its effectiveness, there are several ways in which a firewall can be breached and leave your system vulnerable to attacks.
Here are five ways in which a firewall can get breached:
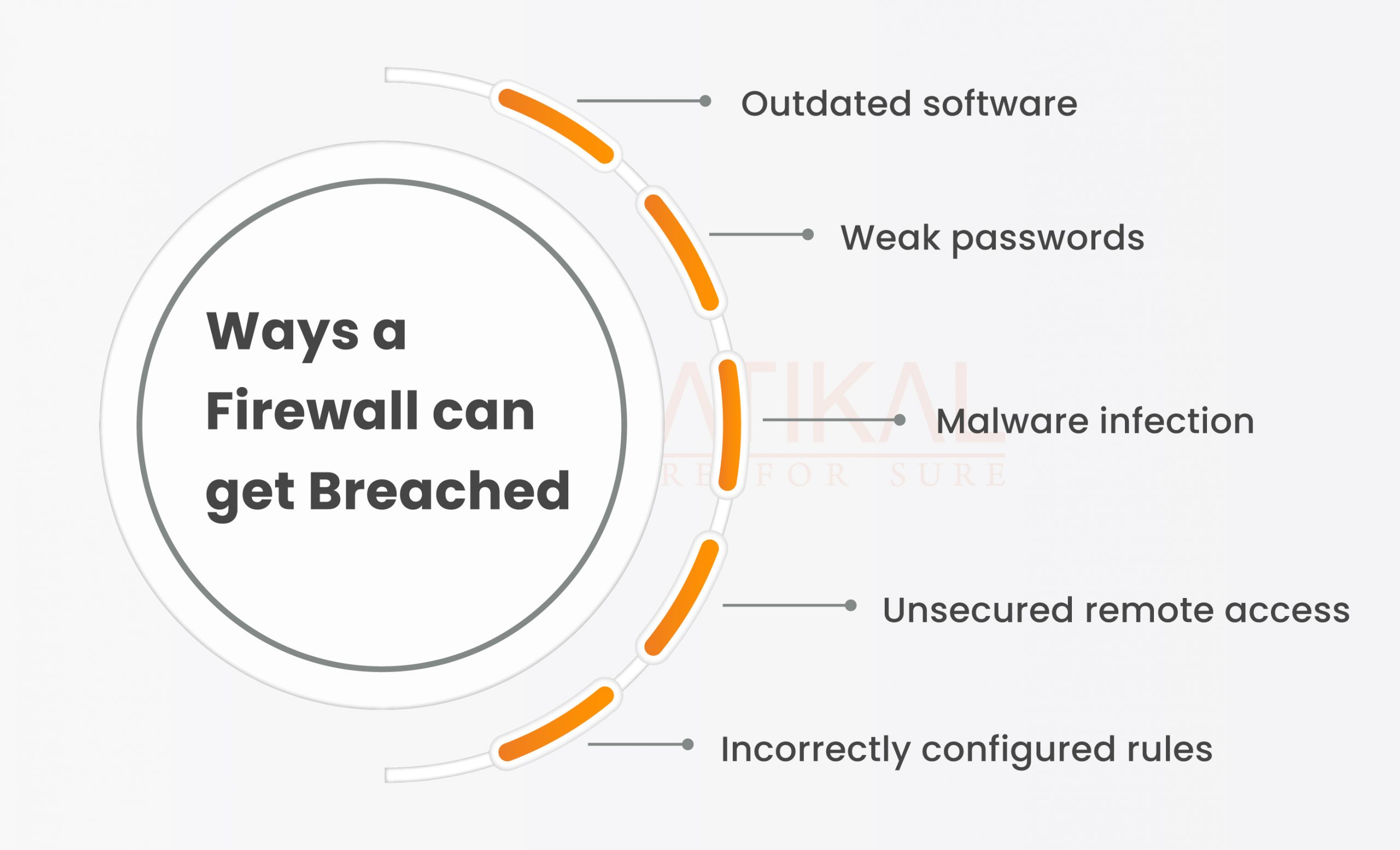
- Outdated software: Firewalls rely on software to function properly, and this software needs to be updated regularly to keep up with the latest threats. If you don’t update your firewall software, it can become vulnerable to attacks that have been discovered since the last update.
- Weak passwords: A strong and unique password is one of the most important ways to protect your firewall from being breached. If you use a weak or easily guessable password, hackers can easily gain access to your firewall and compromise your system.
- Malware infection: Malware is a type of software that is specifically designed to damage or disrupt computer systems. If your system becomes infected with malware, it can potentially bypass your firewall and gain access to your network or computer.
- Unsecured remote access: If you allow remote access to your system, it’s essential to secure this access with a strong password and two-factor authentication. If these measures are not taken, hackers can potentially gain access to your firewall through remote access.
- Incorrectly configured rules: Firewalls rely on rules to determine what traffic is allowed and what is blocked. If these rules are not configured correctly, it can potentially allow unwanted traffic to pass through the firewall and compromise your system.
To protect your firewall from being breached, it’s essential to regularly update your software, use strong passwords, protect against malware infections, secure remote access, and correctly configure your firewall rules.
By taking these precautions, you can help to keep your system secure and prevent cyber threats from reaching your network or computer.
Conclusion
“Despite implementing a firewall, hackers can still find ways to bypass it and access your system. Kratikal services offer various solutions to protect your system from these tactics and keep your data secure.
In conclusion, it is clear that hackers have a number of ways to bypass your firewall using various techniques and tools. However, by using Kratikal services, you can significantly reduce the risk of these attacks and protect your network from cyber threats.
Kratikal, a CERT-IN Empanelled Organization offers a range of security solutions, including firewalls, intrusion prevention systems, and vulnerability management, to help you safeguard your organization from potential hacking attempts. By implementing these measures and staying vigilant, you can effectively protect your business and its sensitive data from cyber threats.
“Protect your network from cyber threats by learning the top methods hackers use to bypass firewalls. Share your thoughts in the comments below.”









Leave a comment
Your email address will not be published. Required fields are marked *