The world is full of machines and gadgets, readily participating in the race to automation, though this race incorporates a hoard of convolutions. IoT is the escape route to push these convolutions at bay, making IoT security testing an essential aspect. The interconnecting machines’ network that supports effortless data exchange is popularly termed IoT (Internet of Things). It is a rapid-growing technology making its significance in almost every sector and has improved the productivity, efficiency, and pliability of the operations and workflow of industries.
In 2018, the global market size of IoT security was valued at $8,472.19 million and it is forecasted to hit 73,918.82 million by 2026, expanding at a CAGR of 31.20%.
No doubt, IoT devices and systems have brought a huge difference, in a positive manner, in the work process of modern-age industries. They also have exposed these industries to significant risks and that’s where the need for IoT security occurs.
Get cybersecurity related information in abundance through our weekly newsletter, and for that matter, you can also jump to Kratikal’s website to quench your information security thirst. Are you worried about hackers bypassing your firewall? In this newsletter, let’s figure out the reason behind it.
Table of Contents
What is IoT Security?
The epoch of hi-tech technologies and IoT devices added value to the operations of the company by elevating productivity, accessibility, and scope for innovation. At the same time, it has raised concerns about the cybersecurity of these devices and technologies.
Nowadays, threat actors can compromise and hack any device from Google Assistant to the smart appliances at your home and hold great power to harm you. For this reason, organizations rendering IoT security testing and prevention remedies have pulled all the limelight.
IoT security is a process of arm-guarding IoT devices and systems with advanced tools to ensure secure data transmission, prevent hacking of the devices, and ensure the data security standards are being followed correctly.
Get in!
Join our weekly newsletter and stay updated
How IoT Security Can Protect Your Business?
Every month, hackers launch more than 5000 cybersecurity malware/attacks targeting IoT devices specifically. Due to this, approx. 60% of small-scale businesses get shut down post being attacked by con artists.
However, seeking IoT security must not cost a fortune to any business organization instead it has to be cost-effective yet efficient and proactive.
These are a few infrastructure utilities that businesses with secured IoT devices and systems leverage:
- Mitigate the probability of hacks and data breaches
- Receive early compliance with respective standards
- Alleviate monetary losses and cost of negligence
- Minimize reputational harm & maintain reliability
- Elevate the security of IoT and the agility of business operations.
If businesses give priority to IoT security, they ensure a range of benefits that ultimately aid in business growth and customer reliability.
Top IoT Security Testing Companies in 2025
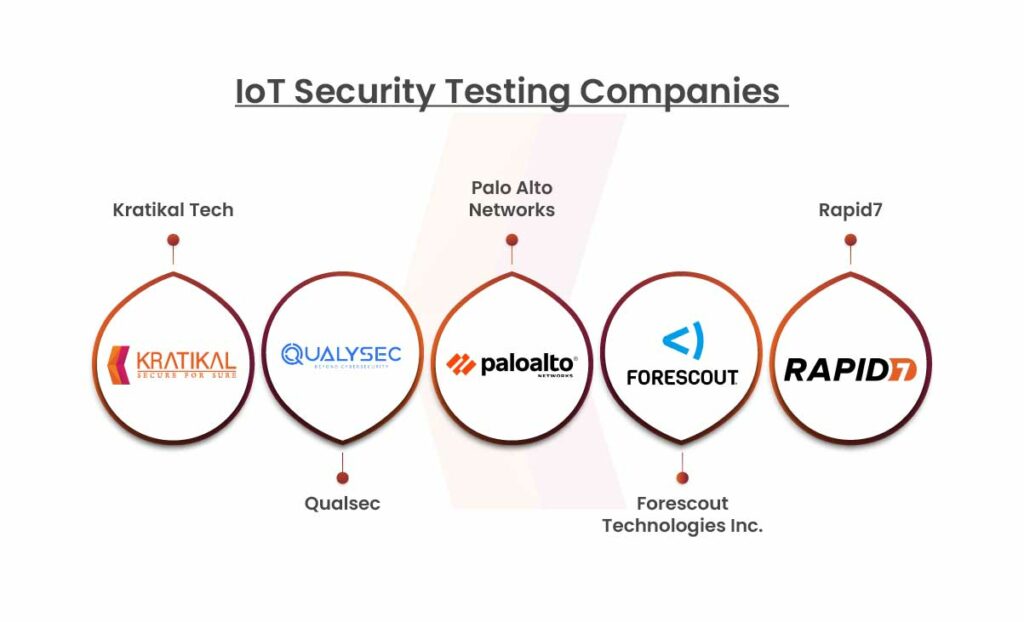
Due to skyrocketing cyber threats towards IoT, organizations must be aware that a lack of IoT security can cause massive losses to their businesses. To ease your job of finding a reliable and efficient IoT security testing company, we have compiled a list of the top 5 IoT testing organizations that can provide you with a detailed report on vulnerabilities in IoT devices and systems along with prevention tips against cyber attacks.
The aforementioned firms have been proven to be reliable sources of cybersecurity solutions and services.
Kratikal Tech
As a CERT-In empanelled auditor, Kratikal is renowned for its expertise in VAPT and compliance services. Our unwavering commitment to excellence and adherence to the highest industry standards are evident through our reputation. Kratikal presently works with 650+ SMEs and enterprises. We have achieved 1000+ weeks of security testing experience along with 100M+ lines of code tested. Kratikal has detected 10,000+ Vulnerabilities. Compliance has been achieved for 200+ organizations. Businesses across diverse industries value Kratikal for its comprehensive approach. We offer a broad range of VAPT Testing and Compliance Services. The Services offered by us are listed below:
VAPT Services
Web Application Testing
Mobile Application Testing
Network Penetration Testing
Cloud Penetration Testing
IoT Security Testing
Secure Code Review
Medical Device Security Testing
Threat Modeling
Root Cause Analysis
Red Teaming
Software Composition Analysis
Compliance Services
Standard Compliance
ISO/IEC 27001 Compliance
SOC 2 Compliance
GDPR Compliance
HIPAA Compliance
PCI DSS Compliance
ISO/IEC 27701 Certification
NIST CSF
ISO/IEC 27018 Certification
Cyber Crisis Management Plan
ISO/IEC 27017 Certification
SDLC Gap Analysis
Regulatory Compliance
IS Audit(RBI)
IRDAI Compliance Audit
SEBI Compliance Audit
CERT-In Security Audit
SAR Compliance Audit
CICRA
IT General Controls
DLA Audit
Qualsec
Qualysec is a trusted cybersecurity company specializing in penetration testing and quality assurance services. With a mission to secure digital ecosystems, they offer tailored solutions to identify and mitigate vulnerabilities across applications, networks, and systems. Backed by a skilled team and innovative tools, QualySec ensures robust security for businesses, fostering trust and resilience in the ever-evolving cybersecurity landscape.
Plato Alto Networks
Palo Alto Networks delivers a comprehensive suite of cybersecurity services and solutions. Its Internet of Things software supports IoT, IoMT, and OT devices, offering advanced security and assessment capabilities. The platform further enhances protection with features such as network segmentation, asset management, vulnerability management, and specialized device security measures.
Foresecout Technologies
The company provides comprehensive visibility and control over connected devices, including IoT, IoMT, and OT systems. With features like automated risk-based segmentation, compliance enforcement, and real-time monitoring, Forescout ensures protection against cyber threats. It also enables seamless device management and lifecycle oversight across diverse network environments.
Rapid 7
Rapid7’s cloud-based security platform helps identify, analyze, and mitigate risks. Its IoT security testing team detects threats and weaknesses in IoT ecosystems, implementing risk-reduction strategies. By conducting penetration and system analysis testing, Rapid7 evaluates devices’ internal architecture and physical security to assess and address the complexity of attack surfaces.
Book Your Free Cybersecurity Consultation Today!
Conclusion
IoT security testing has become a critical priority for businesses across industries. The outlined companies—Kratikal Tech, Qualsec, Palo Alto Networks, Forescout Technologies Inc., and Rapid7—offer comprehensive and reliable cybersecurity solutions, ensuring robust protection against vulnerabilities and cyber threats. By leveraging these trusted services, organizations can safeguard their IoT ecosystems, enhance operational efficiency, and foster customer trust. Ultimately, this will pave the way for sustainable growth and resilience in an increasingly digital world.
FAQs
- Why is IoT security testing crucial for organizations?
With the rising number of cyber threats targeting IoT devices, security testing ensures vulnerabilities are identified and mitigated to protect sensitive data and maintain operational efficiency.
- Are IoT security testing services applicable to all industries?
Yes, industries like healthcare, finance, retail, and technology benefit greatly from these services as they rely heavily on interconnected devices and systems.
- What factors should I consider when choosing an IoT security testing company?
Look for companies with a strong reputation, comprehensive services like VAPT and compliance, proven expertise, and cost-effective yet efficient solutions.









Leave a comment
Your email address will not be published. Required fields are marked *