Now that it has been formally launched, the new ISO 27001 standard is available. The complete name of the standard is ISO/IEC 27001:2022 Information Security, Cybersecurity and Privacy Protection — Information Security Management Systems. Companies must protect operations, sensitive data, and intellectual property from cyber threats. Building corporate resilience demands a timely and flexible strategy in the era of industrialized cyberattacks, where information security risks are always evolving. Information and data power value-added business processes. Nothing in our digital economy operates without information sharing.
Table of Contents
Get in!
Join our weekly newsletter and stay updated
The new ISO/IEC 27001:2022, which places a strong emphasis on process orientation in information security management, is precisely where it comes into play in this situation. The ISO 27001 standard has served as a trusted but outdated foundation for information security management systems for more than two decades. Despite its advanced age, the standard was able to expand in the last year of 2021, as seen by a 32% increase in certificates, according to the ISO Survey. The updated ISO/IEC 27001:2022 was released on October 25, 2022, in response to the rising demand for a modern information security assessment framework. What can we expect?
New Features of ISO 27001
Constantly evolving cyber threats try to attack and compromise information flows and hence corporate processes by making use of fresh potential security flaws in organizations. The threats that this mechanism poses to the three fundamental security objectives of information security—confidentiality, integrity, and availability—must be recognized and controlled. Regardless of an organization’s organizational structure, size, or viewpoint, ISO 27001 outlines the framework for an information security management system (ISMS). Risk management is the key component in this.
- The long-delayed necessity for process orientation is now made the focal point of a successful ISMS through adaptation to the so-called Harmonized Structure in the new ISO/IEC 27001:2022 standard.
- The update addresses best practices for managing various information security vulnerabilities.
- The subsequent pertinent adjustment further underscores the significance of process orientation, which is a feature shared by all HS-based management systems.
In addition to the aforementioned changes, 11 new controls, 24 existing controls that need to be combined, and 58 controls that need to be modified. The new controls are as follows:
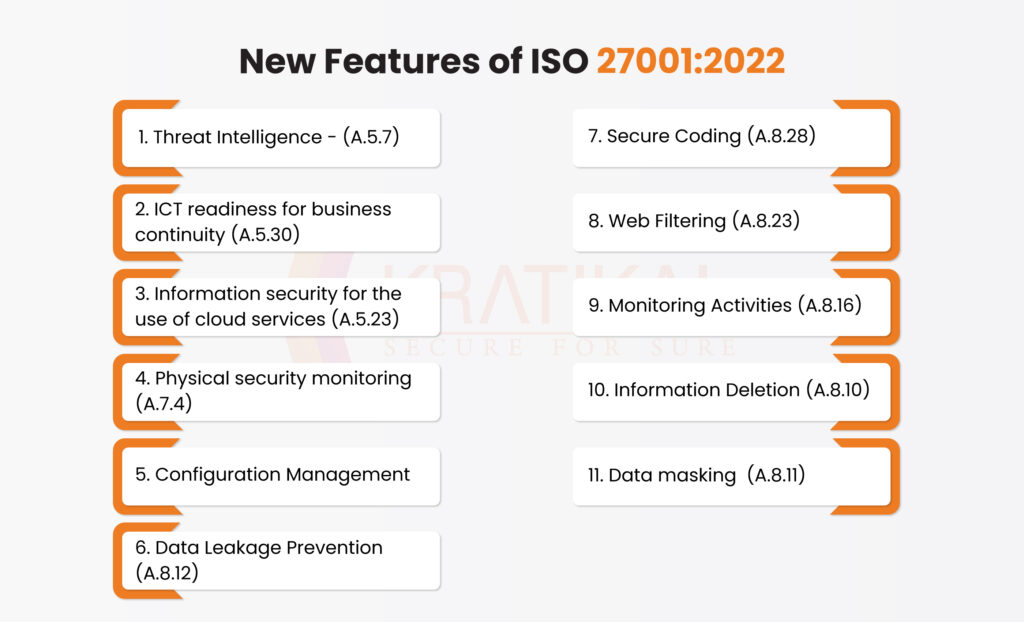
- Threat Intelligence – (A.5.7) – Organizations will need to take proactive measures to find dangers. Risk evaluations, context, and recognizing risks and opportunities will all be connected to this.
- ICT readiness for business continuity (A.5.30) – The emphasis is now firmly on ICT, even though this is similar to earlier business continuity controls.
- Information security for the use of cloud services (A.5.23) – Since 2013, there has been a substantial increase in cloud computing, therefore this feature is highly appropriate.
- Physical security monitoring (A.7.4) – Physical security must now be constantly checked.
- Configuration Management – The management and recording of configuration is now required.
- Data Leakage Prevention (A.8.12)– A concluding GDPR/DPA 2018-related control that strengthens controls.
- Secure Coding (A.8.28) – This has been strengthened while still being connected to earlier development controls, particularly read and write access and libraries, etc.
- Web Filtering (A.8.23) – With the expansion of the internet, it is more crucial than ever to protect yourself from malicious or hostile websites.
- Monitoring Activities (A.8.16) – A stricter interpretation of the standard’s monitoring requirements.
- Information Deletion (A.8.10) – In connection with recent rules and laws like GDPR and DPA 2018, stricter controls are required for information erasure.
- Data masking (A.8.11) – Pseudonymization and anonymization are now often used as a result of GDPR and DPA 2018.
A Few Things Needs Attention
- Timeline – The transition to ISO/IEC 27001:2022, for organizations that are currently ISO/IEC 27001:2013 certified, will take three years.
- Transition Requirements for Organization – They outline the steps that must be taken in order for organizations that are already certified to ISO/IEC 27001:2013 as well as those who are thinking about certification in the future to transition to and/or obtain certification against the ISO/IEC 27001:2022 standard.
- Transition Requirement for Accreditation and Certification Bodies – The document also specifies the transition procedures that accreditation bodies (ABs) and their accredited certification bodies (CBs) must follow to upgrade their accreditations to reflect the ISO 27001 standard’s 2022 revision.
- Updated Control Set – The primary modification made by the update was the substitution of the control set from ISO/IEC 27002:2022 for the previous control set from ISO/IEC 27001 (known as “Annex A”) in that standard.
Steps for the organization already certified –
The following are the primary actions to take as part of the subsequent steps:
- Purchasing the revised Standard.
- Examine the control modifications in the new ISO 27001 Standard.
- Make a risk assessment or analysis.
- The most appropriate controls should be chosen to reduce any risks that have been identified, and your ISMS policies, standards, etc. should be updated as necessary.
- Keep your Statement of Applicability current.
Boost Your Attitude Towards Information Security
Adopting cyber resilience helps organizations gain a competitive edge and swiftly become industry leaders. The new ISO/IEC 27001 ensures that your entire organization, not just your infosec team, is covered, supports your digitization plan, lowers the risk of breaches, and increases customer confidence in your brand and information resilience in your organization.
When it comes to assisting you with understanding the changes, determining their influence on the security goals of your company, providing implementation advice, and migrating your certification, Kratikal’s CERT-In Empanelled platform and tools are ready to help you right away. We offer security auditing for Compliance, including PCI-DSS, ISO/IEC 27001, GDPR, HIPAA, and others, in addition to our VAPT services.
FAQs
- What are the key changes in ISO/IEC 27001:2022?
Key changes include process orientation, adaptation to the Harmonized Structure (HS), 11 new controls, 24 combined controls, and 58 modified controls, emphasizing modern security measures like threat intelligence, secure coding, and data leakage prevention.
- Which versions of the ISO standard does the update replace?
ISO/IEC 27001:2022 replaces ISO/IEC 27001:2013 and introduces a new control set based on ISO/IEC 27002:2022, known as “Annex A.”









Leave a comment
Your email address will not be published. Required fields are marked *