Injection attacks distinguish themselves among these threats as devastating exploitation. Businesses face a variety of cyber risks in today’s interconnected digital environment that might jeopardize their operations. This also compromises sensitive data and results in substantial monetary losses. India experienced an 18% increase in weekly attacks on average during the first quarter of 2023 compared to the same period in 2022, with 2,108 attacks per organization per week.
For businesses of all sizes, it is vital to understand the seriousness of injection attacks. Legal liabilities, reputational harm, a loss of confidence from clients, and the disruption of vital activities can all have huge financial ramifications. Organizations may proactively set up robust safety measures. This is done to defend their digital assets and protect against the underlying risks involved with injection attacks.
This blog would elaborate on the important topic of injection attacks by looking at their effects on businesses. You would understand explaining the factors that contribute to their prevalence and outlining practical ways to reduce the cyber risk.
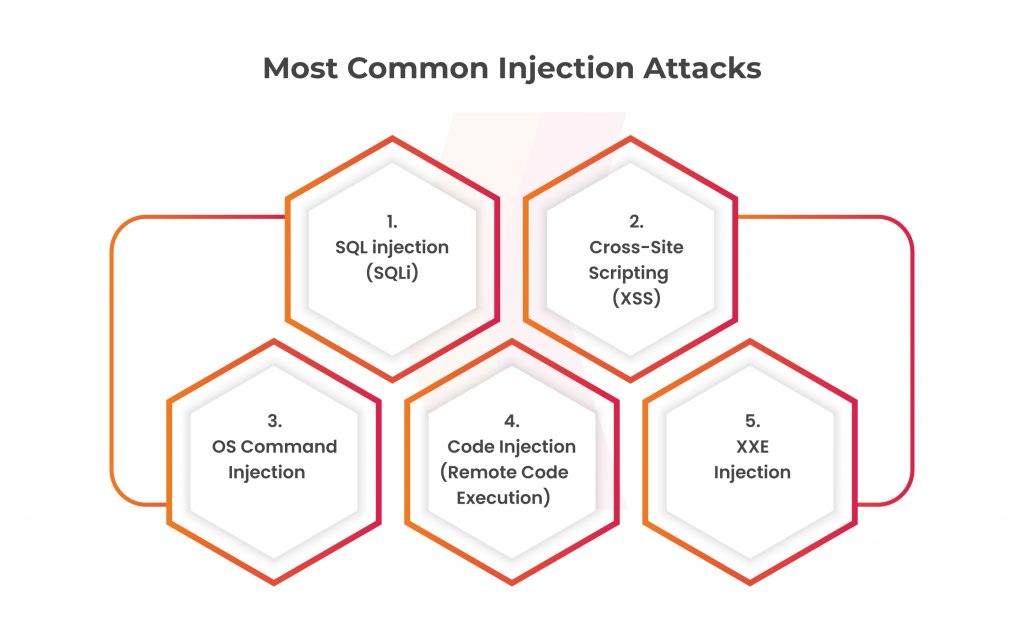
We will look at the most prevalent kinds of injection attacks, such as SQLi, XSS, code injection, and many more. We will explore how these attacks might affect businesses, presenting examples to demonstrate how serious the issue is. Additionally, we’ll go through reliable preventative measures and recommended practices to lessen the risks of injection attacks. This gives organizations the tools they need to strengthen their defenses and fend off possible attacks.
Table of Contents
Dark Side of Injection Attacks on Business
Due to a major flaw in their systems, businesses can seriously be threatened by injection threats. These attacks make use of flaws in operating systems, databases, or online applications. This is done to allow hostile actors to insert and run unauthorized code or commands. A successful injection attack can have disastrous results and wide-ranging repercussions for the targeted company and its clients.
Leading cybersecurity organizations’ research has uncovered alarming figures on the impact of injection attacks on businesses. In a recent study, in which more than 60% of the firms polled, encountered a serious security incident. This took place because of injection attacks in the previous 12 months. These occurrences caused significant financial losses, unfavorable legal outcomes, and reputational damage to the concerned companies.
The most prevalent suspects of injection attacks that could affect your application are SQL injection and Cross-Site Scripting. However, it’s important to be aware of the wider variety of injection attacks, each with a unique set of objectives and exploitation methods. The following are some of the most common injection attack types to be aware of:
SQL Injection Attacks (SQLi)
For businesses of all sizes, SQL injection continues to be one of the most prevalent and hazardous types of cyberattacks. SQL injection primarily entails taking advantage of flaws in input fields of online applications that interact with backend databases. Attackers can insert malicious SQL code into the application’s database query by changing user inputs. This will change the application’s intended behavior. Unauthorized access to sensitive data, data manipulation or deletion, and even total system compromise are all possible outcomes of this unauthorized code execution. Attacks using SQL injection can have devastating impacts on enterprises.
One of the oldest and most dangerous web-based application vulnerabilities is SQL injection. SQL injection is ranked #6 in the CWE Top 25 for 2021 and is identified as CWE-89: Improper Neutralisation of Special Elements Used in a SQL Command.
Cross-Site Scripting (XSS)
XSS attacks are a sort of injection, in which malicious scripts are injected into websites that are otherwise safe and reliable. XSS attacks occur when a threat actor utilizes a web application to transmit malicious code to a separate end user, typically in the form of a browser-side script. To exploit an XSS vulnerability, the attacker delivers a text string with malicious code, such as by inserting it into the URL as the user ID parameter. The attack code is then executed by the victim’s browser rather than being viewed as a regular parameter value.
Attackers can influence how the victim’s browser interprets and executes the code by inserting malicious scripts into the application’s output. This might result in unauthorized activities or data disclosure. The three basic categories of XSS attacks are stored (permanent), reflected (non-persistent), and DOM-based.
Get in!
Join our weekly newsletter and stay updated
XSS has been identified as the second most risky software vulnerability in the CWE Top 25 for 2021 and is classified as CWE-79: Improper Neutralisation of Input During Web Page Generation. Several other types of XSS vulnerabilities, such as stored (permanent) XSS and DOM-based XSS, are to be taken into account.
OS Command Injection
The reliability and functioning of online applications are put at risk. This is happening to the significant security vulnerability known as OS Command Injection. This type of attack happens when a user-supplied command may be directly executed on the underlying operating system. Malicious actors may inject and carry out unauthorized orders by taking advantage of this vulnerability, potentially compromising the entire system.
OS command injection, also known as CWE-78: Improper Neutralisation of Special Elements Used in an OS Command, was ranked #5 on the CWE Top 25 list. Blind command injection and out-of-band command injection are two examples of the several command injection vulnerabilities that should be detected.
Code Injection (Remote Code Execution)
Code Injection, or more specifically Remote Code Execution (RCE), is a major security vulnerability. This jeopardizes the integrity and confidentiality of web applications. This kind of attack allows hostile actors complete access to and control over the target machine. This is done through remotely injecting and executing arbitrary code. In this section, we examine the workings of code injection (RCE), probable repercussions, and countermeasures to this serious issue.
Under CWE-94: Improper Control of Code Generation, code injection is listed. Numerous programming languages and frameworks are covered by the detection of dozens of code execution and code evaluation vulnerabilities.
Strong security controls must be put in place to avoid code injection. Validate and fix up all user input to make sure a threat to the code isn’t present. When communicating with databases, use prepared statements and parameterized queries.
XXE Injection
Strong security measures that reduce the possibility of code injection must be included in online applications to ensure robust security. A risk like this is known as XML External Entity (XXE) Injection. Here the attackers use the processing of XML data to inject malicious entities, possibly exposing data. This causes server-side request forgery (SSRF), or even execution of remote code.
CWE-611: Improper Restriction of XML External Entity Reference is an indicator for attack vectors involving XML external entities. XXE injection was ranked #4 in the OWASP Top Ten for 2017. However, in 2021, it was combined with the Security Misconfiguration category. All user input, especially XML input, must be validated and sanitized before processing to prevent XXE Injection attempts. Strict checks should be included for input validation to spot and reject any potentially dangerous or incorrectly formatted XML entities.
Preventive Measures for Injection Attacks
Organizations may significantly reduce the risks of injection attacks by putting these preventive measures in place. Maintaining a robust and secure web application environment requires regular monitoring, testing, and keeping up with new threats.
- Regular Security Audits and Updates: Conduct frequent security audits to find vulnerabilities. Install the appropriate patches and upgrades to the software components utilized in the application.
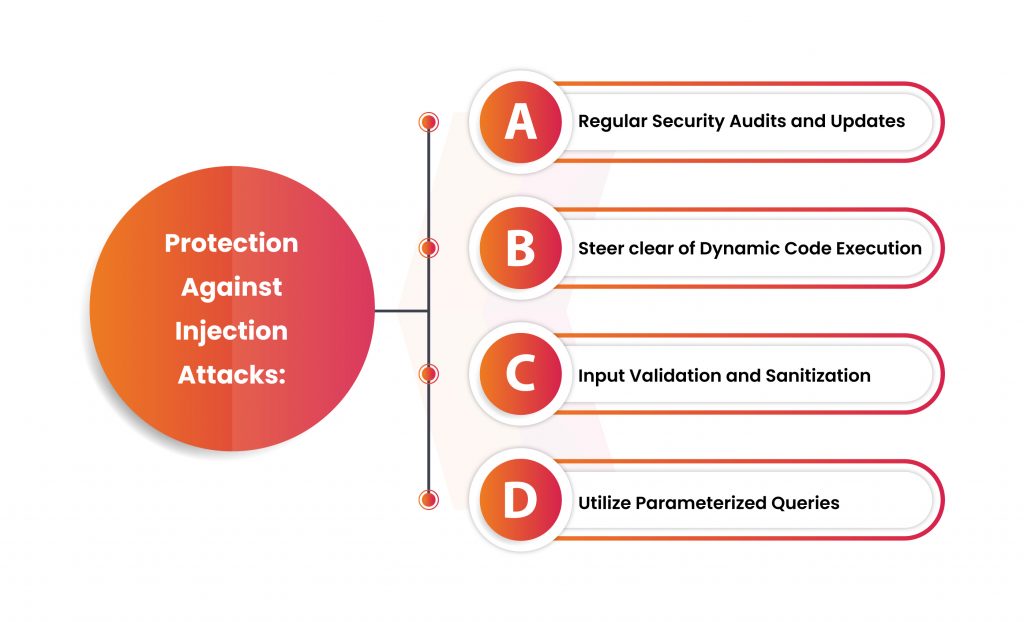
- Steer clear of Dynamic Code Execution: Reduce or avoid the use of eval() or comparable functions. This enables the dynamic execution of user-supplied code. The probability of injection attacks dramatically increases when code is generated dynamically from user input.
- Input Validation and Sanitization: Validate and sanitize all user input completely. This is done to make sure it follows the desired formats. The code should be free of malware and other special characters. Put strong input validation procedures in place, and clean up user input by eliminating or escaping potentially dangerous characters.
- Utilize Parameterized Queries: Use parameterized queries or prepared statements when interacting with databases or running queries. By separating data from executable code, organizations can stop attackers from inserting malicious code directly into the query.
Conclusion
Organizations must put strong security policies in place to reduce the risks brought on by injection attacks. To make sure that user input is free of malicious code, carefully input data validation and ensure sanitization. When working with databases, using parameterized queries and prepared statements can prevent attackers from inserting harmful code or commands.
Kratikal, a CERT-In empanelled organization can help businesses avoid injection threats. We can assist in locating and fixing vulnerabilities in online applications with our expertise in vulnerability assessments. We also assist in penetration testing and secure development techniques. Security awareness programs and fostering security-conscious mindsets within organizations are also part of our solutions.
Businesses may strengthen their defenses against injection attacks, and protect their digital assets, and client trust. This will also build their reputation by putting these preventative steps into place. Businesses can also collaborate with a reputable cybersecurity firm like ours. To maintain a continued defense against injection attacks and other cyber threats, be watchful. Make sure to have routine upgrade security procedures, and stay aware of emerging risks.








Leave a comment
Your email address will not be published. Required fields are marked *