Apache OpenMeetings is an open-source application. Users employ it for web conferencing, presentations, and other collaborative work. However, researchers have identified several network security vulnerabilities that malicious actors might exploit. These vulnerabilities can be utilized to take over admin accounts and install malicious software on vulnerable servers. There is a need to fix potential security flaws that can jeopardize data confidentiality. This also threatens the data integrity of these virtual interactions that come with their broad utilization.
We will be looking at the serious network security flaws affecting Apache OpenMeetings in this blog. Both users and administrators must be aware of these vulnerabilities. By taking the appropriate measures, users can protect sensitive data and maintain a secure virtual environment. It is essential to be proactive in implementing security protocols and best practices to safeguard valuable information and ensure a safe online experience.
Table of Contents
Instances for Cyber Attackers to Hijack Vulnerability
Cyber attackers bring applications to a vulnerable state where they can take advantage of the user’s account. Three Apache OpenMeetings bugs – CVE-2023-28936, CVE-2023-29023, and CVE-2023-29246 could enable malicious attackers to hijack an administrator account. This vulnerability enables remote execution of identified arbitrary code, necessitating immediate action to prevent unauthorized access and protect data integrity.
In addition to linking meeting invitations with a particular room and user, OpenMeetings also generates a unique hash that it utilizes to access the invitation data. The second problem allows attackers to gain full access to a session, while the first of the three flaws enables hackers to enumerate valid invitation hashes and redeem them.
Cybersecurity company emphasizes that a self-registered hacker might use a chain of these vulnerabilities to hijack the instances. This is done to get remote code execution on the underlying server. Poor session management, inadequate authentication procedures, or insufficient access controls can all contribute to these network security vulnerabilities. By exploiting this vulnerability, hackers might operate as legitimate users. This enables to obtain access to private data or disrupting meetings without authorization.
Get in!
Join our weekly newsletter and stay updated
Apache OpenMeetings Bugs
CVE-2023-28936- Weak Hash Comparison
This vulnerability exists as a result of the use of the GetByHash method. This enumerates all invite hashes on the OpenMeetings application by querying the Invitation object from the database by user-provided hash using the LIKE operator, which accepts wildcard values.
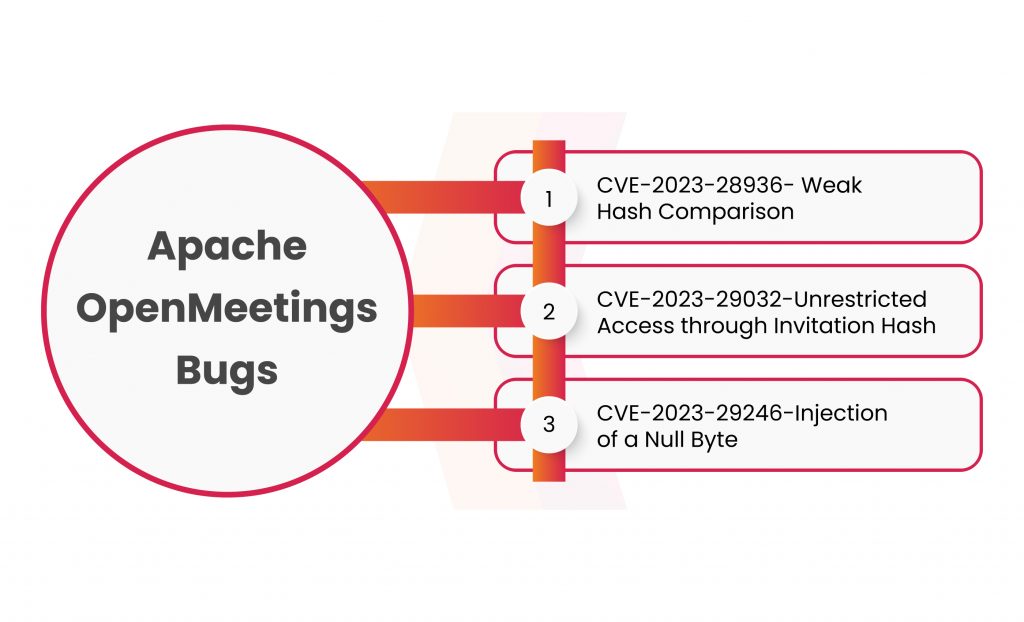
CVE-2023-29032-Unrestricted Access through Invitation Hash
This flaw exists since if no room is specified while being supplied to the set user, the rights set inherits the invited users’ rights.
CVE-2023-29246-Injection of a Null Byte
When a threat actor has administrative access to OpenMeetings, they can use null-byte injection. This is done to run remote code on the server.
Apache has corrected this vulnerability, and Apache OpenMeetings 7.1.0 includes a fix for it. Users are encouraged to update to the application’s most recent version to fend off threats.
Strategies for Mitigation Against Hijack Attacks
Consider implementing the following network security precautions to protect your OpenMeetings installation from instances of hijack attacks:
Strong Authentication Mechanisms: To prevent unauthorized access to meetings, mandate using strong authentication techniques like multi-factor authentication (MFA).
Regular Upgrades and Patches: To address known security vulnerabilities, keep your OpenMeetings software up to date with the newest patches and upgrades.
Access Controls: Put in place rigorous access controls to only allow authorized attendees into meetings, reducing the risk of unauthorized access.
Monitor User Activities: Monitor user activity throughout sessions at all times, and cut off any suspicious connections immediately to stop hijacking attempts.
Contributing Factors for Server Code Execution Vulnerability
Consider the following recommended practices for enhancing Apache OpenMeetings’ server code execution security:
- Implement strong input validation and output encoding to prevent attempts at code injection by malevolent users.
- To find and address potential application vulnerabilities, conduct routine network security audits and assessments.
- Emphasize secure coding practices among developers to avoid frequent coding mistakes that could result in network vulnerabilities.
- Install firewalls and intrusion detection systems to track incoming and outgoing network traffic, identifying unusual activity, and preventing it.
Conclusion
In conclusion, even though Apache OpenMeetings provides a solid base for online meetings and collaboration, it is critical to be on alert for any possible vulnerabilities. The serious issues that need users’ and administrators’ quick attention and action are instance hijack and server code execution.
Businesses can significantly enhance the network security posture of the Apache OpenMeetings installation by adhering to the suggested mitigation measures and best practices outlined in this blog. This proactive approach will not only safeguard confidential information but also ensure everyone attending your virtual meetings can do so in a secure and productive setting.
Just keep in mind that maintaining a secure virtual meeting environment requires staying up to date on the most recent network security trends and changes.
Protect the reliability of your online associations by taking control of your OpenMeetings security immediately!







Leave a comment
Your email address will not be published. Required fields are marked *