Table of Contents
Introduction
Technological advancements reshape daily life and redefine digital interactions. Among these technological swifts, Web3 Security has stood out as a game-changer. It is promising a decentralized future and revolutionizing how we create and use online platforms and apps. Web3, enabled by blockchain and decentralization, presents exciting opportunities for a user-centric, secure, and open internet. However, this new paradigm also has a unique set of obstacles, especially regarding cybersecurity. Protecting digital assets and maintaining data privacy becomes vital as the Web3 ecosystem develops and grows. The distributed nature of Web3 platforms and the intricate cryptographic processes necessitate the need for strong security.
We will make our way through the complexities of Web3 in this blog. We’ll explore various aspects of this evolving topic, including blockchain fundamentals and advanced security measures for enhancing Web3 platforms and applications.
In this blog, we delve into the fundamentals, covering decentralized identification, smart contract vulnerabilities, secure key management, and privacy-enhancing solutions. We can better understand the security issues Web3 platforms confront and traverse the changing threat landscape by comprehending these principles.
Discover essential best practices for enhancing security in the Web3 ecosystem, applicable to organizations, consumers, and developers.
I. Significance of Web3 Security
This blog aims to provide the necessary information and resources for safely navigating the Web3 environment. Together, we can foster the growth of the Web3 ecosystem, ensure a secure digital future, and gain a deeper knowledge of Web3 security complexities, issues, and solutions.
In the rapidly evolving world of Web3, where decentralized technologies like blockchain are gaining popularity, it is crucial to grasp the significance of Web3 security. Decentralized applications, smart contracts, and digital wallets are all protected from dangers and vulnerabilities utilizing web3 security. Individuals may effectively traverse this environment and safeguard their digital assets and data privacy by understanding the fundamentals of Web3 security.
Decentralized apps, which provide a variety of features and services, are at the forefront of Web3 innovation. They do, however, also provide particular security difficulties. Since decentralized applications (dApps) depend on blockchain networks, it is crucial to examine the security of the underlying blockchain protocols and consensus processes. This examination aids in spotting potential weaknesses and ensuring the decentralized ecosystem’s stability.
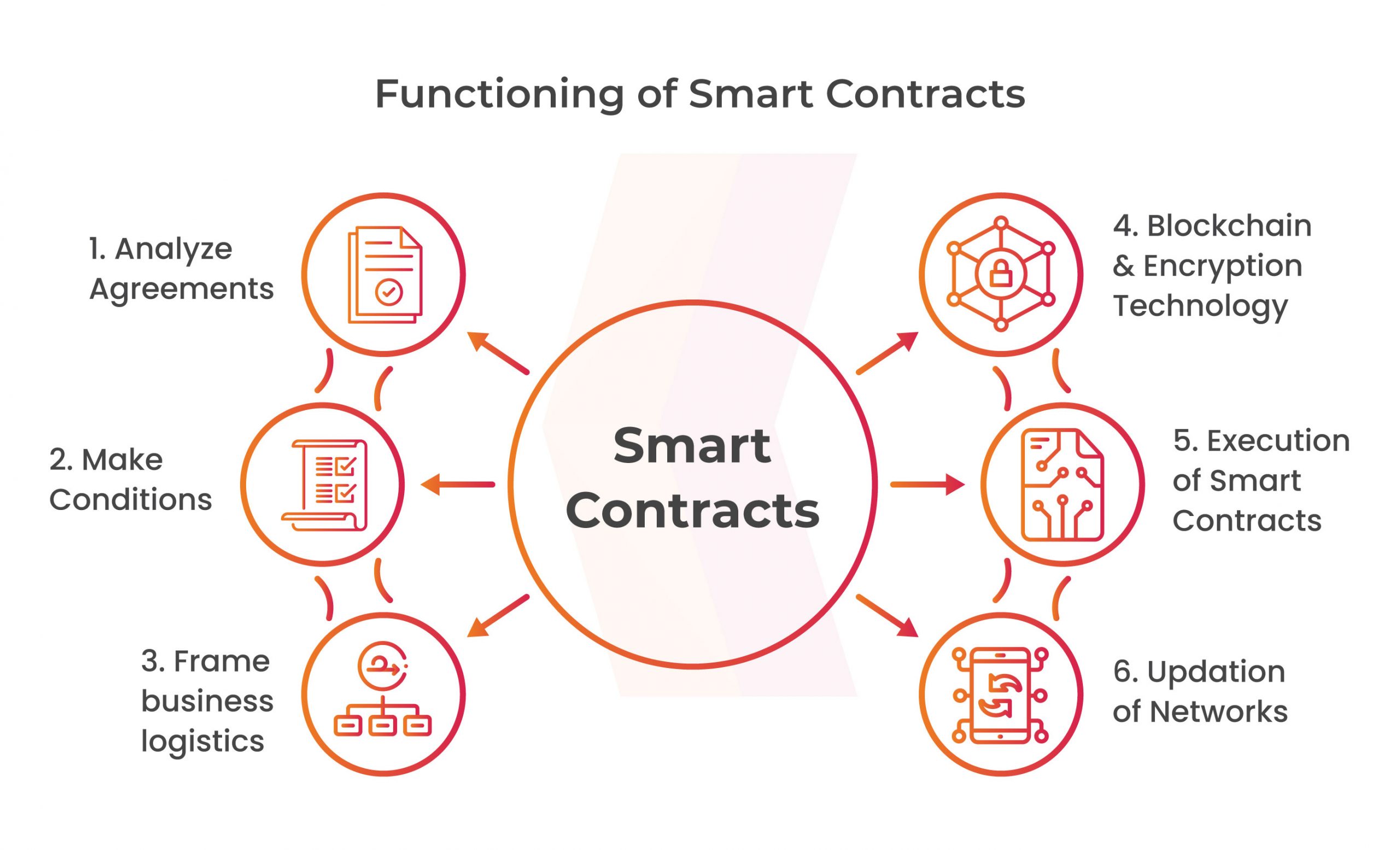
Many apps depend on smart agreements, which are self-executing contracts with predefined rules. Smart contract errors or vulnerabilities, however, have the potential to be exploited or result in substantial financial losses. Consequently, it is of the utmost importance to understand smart contract security. This entails using secure coding techniques, doing formal verification to spot any problems, and routinely checking smart contracts for flaws.
II. Securing Digital Assets in Web3 Security
Vulnerability Assessment and Penetration Testing (VAPT) is a useful procedure to ensure the efficacy of Web3 security. VAPT entails methodically identifying potential vulnerabilities in the Web3 ecosystem, which includes dApps, smart contracts, and digital wallets. Individuals can improve their overall security posture by conducting thorough assessments. They can work with penetration testing to proactively find and address vulnerabilities.
Get in!
Join our weekly newsletter and stay updated
In Web3 security, digital assets like cryptocurrencies and tokens that are (NFTs) have become extremely popular. But when their worth rises, hackers find them to be tempting targets. Adopting strong security measures is essential for protecting your digital assets. This section will examine many methods for protecting digital assets, such as:
Digital wallet security: It’s essential to protect your digital wallet properly. We will talk about the best practices, like using hardware wallets, setting up multi-factor authentication, and updating software.
Auditing of smart contracts: Decentralized apps that use smart contracts are vulnerable. We will go into detail on how crucial it is to perform rigorous audits, spot potential hazards, and use security tools to improve the dependability of smart contracts.
III. Preserving Data Privacy in Web3 Security
The Web3 ecosystem is particularly concerned with the confidentiality of information. Engaging in multiple Web3 activities can expose individuals’ personal information, potentially leading to its public disclosure. This section will concentrate on protecting data privacy in Web3, highlighting important elements like:
Anonymous Transactions: These transactions are privacy-focused cryptocurrencies and protocols that allow for anonymous transactions while safeguarding user identities.
Decentralized Identity Solutions: DID solutions enable people to securely control and maintain their digital identities.
Encryption and Privacy Tools: Implementing tools for strengthening privacy and encryption can greatly improve data privacy in Web3.
Conclusion
Finally, as we discuss the constantly changing technological landscape, the idea of Web3 security becomes a top priority. The security and integrity of these systems are becoming important as blockchain, decentralized applications, and smart contracts become more widely used. This is where Kratikal, a reputable cybersecurity firm, can enter the picture and contribute essential knowledge.
With a wide range of solutions to reduce online dangers and protect sensitive data, Kratikal has become a reputable name in the cybersecurity industry. Our knowledge is much more important now that Web3 security has come into the picture.
Specialized skills and equipment are required to address the particular security concerns posed by decentralized Web3 applications.
Web3 security includes several features, such as protection against smart contract flaws, security of decentralized networks, and protection of digital assets held on blockchain-based platforms. With Kratikal’s expertise in Vulnerability Assessment and Penetration Testing (VAPT), it’s possible to spot possible vulnerabilities in Web3 systems and offer useful information for enhancing security measures.
Kratikal, a CERT-In empanelled auditor, can be crucial in the Web3 security landscape by utilizing their experience in VAPT. We may carry out thorough audits of decentralized software and smart contracts to make sure there are no vulnerabilities that could be exploited.
Kratikal’s proactive approach to cybersecurity and expertise in VAPT and cybersecurity make it a potentially significant player in assuring Web3 security. The comprehensive strategy and commitment to staying on the cutting edge positions us as the perfect partner for organizations seeking to safeguard their Web3 infrastructure. With Kratikal, companies can fully embrace Web3’s potential, ensuring user confidentiality and protecting digital assets.









Leave a comment
Your email address will not be published. Required fields are marked *