A new encryption ransomware named Sodin (or Sodinokibi) or REvil has been discovered which exploits a vulnerability that has been recently discovered in Windows for getting elevated privileges in an infected system. The ransomware was initially distributed by exploiting a vulnerability in Oracle Weblogic. The computers that were infected with the ransomware were left with a note that demands $2500 worth of Bitcoin from every victim. The ransomware leverages the architecture of the central processing unit (CPU) for avoiding detection. This is a functionality that is not frequently seen in ransomware.
The Sodin ransomware is a type of malware that uses the CPU architecture to hide within the system. Sodin is a part of ransomware as a service (RaaS) scheme meaning that its distributors have the freedom to choose the way in which encryption malware should propagate. It includes a functionality that allows malware authors to decrypt files without letting their affiliates know by using a master key which is independent of distributor’s key and is normally used for decrypting the files of the organisations that pay ransom.
Researchers have observed a rise in the number of attacks that involve the Sodin encryptor because of significance of the amount of resources that are required to build such malware. Most of the targets of Sodin ransomware were found in the Asian region with 17.6 percent of attacks in Taiwan, 9.8 percent in Hong Kong and 8.8 percent in the Republic of Korea. The other countries that have suffered from such attacks include North America, Latin America as well as Europe.
Sodin ransomware exploits a zero-day vulnerability called CVE-2018-8453 that the ransomware uses and has been exploited by the FruityArmor hacking group. This vulnerability exists in Windows when the Win32k component is not able to handle objects within the memory, aka “Win32k Elevation of Privilege Vulnerability.” This vulnerability affects Windows Server 2012 R2, Windows 7, Windows RT 8.1, Windows Server 2008, Windows Server 2012, Windows Server 2019, Windows 8.1, Windows Server 2016, Windows Server 2008 R2, Windows 10, Windows 10 Servers etc.
How does Sodin ransomware work?
Initially, attackers configured the initial stage of Trojan that was distributed with encrypted form and configuration block that contained settings and the data. For encrypting victim’s files and the keys for it, attackers have employed the Salsa20 symmetric stream using an elliptic curve asymmetric algorithm.
Once the Trojan is launched, it generates another pair of elliptic curve session keys in which the public key of this pair is saved in the registry using the name pk_key whereas the private key is encrypted using ECIES algorithm and is stored in the registry under the name sk_key.”
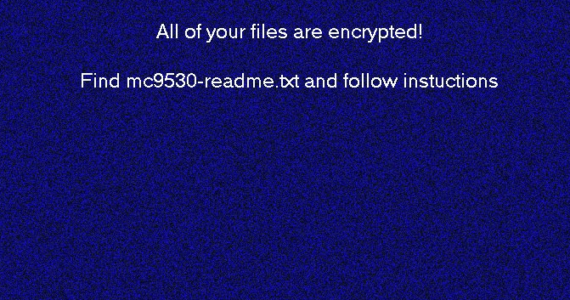
Once the ransomware starts the encryption process, it generates the new pair of elliptic curve asymmetric keys and the symmetric key will encrypt the content of the victim’s file with the Salsa20 algorithm. Once the process of the encryption of files is completed, the new extension will be applied to every file while saving the ransom note next to it when malware-generated wallpaper is being set on the desktop.
Trojan sends the information about the infected machine to attacker’s command and control server and the sending data is encrypted too. Victims are provided with the information about the website where the attackers instruct them to pay the ransom by following the step to recover the decryption key for unlocking the encrypted files.
Sodin ransomware uses a technique called “Heaven’s Gate” allowing the execution of malicious program from a 32-bit to 64-bit code running process, thus, making the detection even more difficult. The technique is used for making analysis of the malicious code more difficult since most of the code examiners support this technique and are therefore unable to identify it. This technique enables ransomware in evading detection using emulation-based detection. It is widely used for discovering previously unknown threats by launching code that behaves suspiciously in a virtual environment that resembles a real computer.
How to prevent ransomware attack like Sodin?

- Organizations should ensure that their software are regularly updated to the most recent versions since regular patches and updates are released in the market.
- Security testing services such as vulnerability assessment and penetration testing services and patch management capabilities may help to automate these processes, they added.
- Implementing a cyber security awareness and training program for employees helps them to learn about different methodologies that are employed in cyber-attacks. With tools like ThreatCop, organizations can strength their human line of defence by using simulated attacks and customized learning modules that are based on them.








Leave a comment
Your email address will not be published. Required fields are marked *