A decade ago, the ‘spray and pray’ method was extremely popular for sending out phishing emails. This involved sending a generic email asking victims for credentials including passwords, credit card numbers etc. These mails were sent to as many users as possible. With the advancement in security measures, email services can easily block such attack tactics. This has led to the advancement in modus operandi of phishing attacks. Attackers are deploying phishing attacks that are target-specific in nature.
In a new wave of phishing attacks, attackers have been leveraging the server-parsed HTML capability (also known as “server-side includes” or “SSI”) as the base for cyber-attacks. Usually, when you request a page from a server, it sends file’s content in the original state as it is stored. The server does not look at the content of the file. However, with server-parsed HTML, server can look as well as manipulate the file’s content such as putting another file’s content, an environment variable’s or the output of a program within the page.
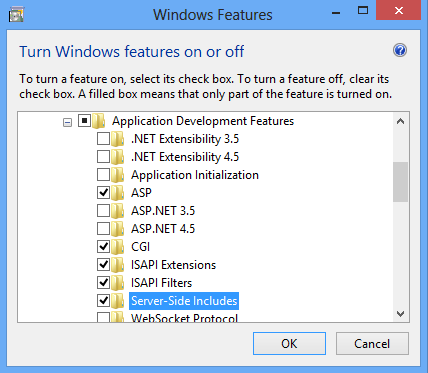
With Server-parsed HTML:
- Maintenance of large sites becomes easier for including standard headers, footers as well as other information in your files. One can edit a file to modify a set of pages.
- Pages can become more dynamic without the requirement of generating pages with Tcl, C, CGI or any other programs. You can also include dynamic information such as the current time or output from a program into your pages.
- This capability enables attackers to victimize users through attachments in emails. In this attack, there is no need to download the attachment. The user redirects to malicious site as soon as he clicks on the attachment. The user reveals his sensitive and personal information by submitting the credentials.
This phishing attack uses SHTML file attachments with JavaScript code. This will allow the disguise of unsafe URL so that it stays hidden away from the user. UK (55%), Australia (31%) and South Africa (11%) are the biggest targets of this new form of phishing attack. While, the finance, accounting and higher education sectors being its biggest victims.
How can we prevent such phishing attacks?
- Enforce per-user outbound rate limits in order to detect the abuse of compromised webmail email account. This will help in slowing down the outbound spam rate as well as, identify and stop the abuse of the email entirely.
- Enable strong spam filters for preventing phishing emails from reaching employees within the organization and to authenticate inbound email using technologies like SPF, DMARC and DKIM to prevent email spoofing.
- A very effective approach is to educate employees about various cyber attacks with security attack simulator and awareness tools like Threatcop. The tool helps in upgrading employees’ defence with its 4-step simulation and awareness cycle.
The increasing sophistication in phishing attacks calls for newer and more advanced cyber security measures that can help in evading such cyber threats. Rather than relying on traditional security measures, adopt a proactive approach that can help in preventing the organization against cyber attacks.








Leave a comment
Your email address will not be published. Required fields are marked *