As we know that modern organizations are moving away from traditional on-premises software and accompanying infrastructure in favor of software as a service offering. According to AMR’s most recent analysis, the Software as a Service (SAAS) market will generate $702.19 billion by 2030 (Report from Allied Market Research). By handling both software and hardware management and system security, Software as a Service (SAAS) companies have liberated customers from these tasks.
When it comes to lowering operational costs, decreasing deployment times, and lowering capital expenditures (CAPEX), SAAS offers appealing, and frequently necessary solutions. All these factors are crucial for enhancing corporate agility. We need to understand what SAAS is first, though, before delving too far into the SAAS-based cyber security issues.
Table of Contents
What is SAAS?
To safeguard customer data in cloud-based software and other information assets, Software as a Service (SAAS) providers establish rules and regulations. To put it another way, SaaS, or Software as a Service, is a cloud-based software distribution approach in which customers buy or access apps online, mainly using a web browser. To ensure the solution operates as intended, a provider manages the application software, middleware, and hardware.
We will outline the main problems or challenges with SAAS-based services in this blog and then elaborate on them so that you may better grasp what they are.
SAAS Security Concerns
The few security issues that every firm must take care of for SAAS-based services are listed below:-
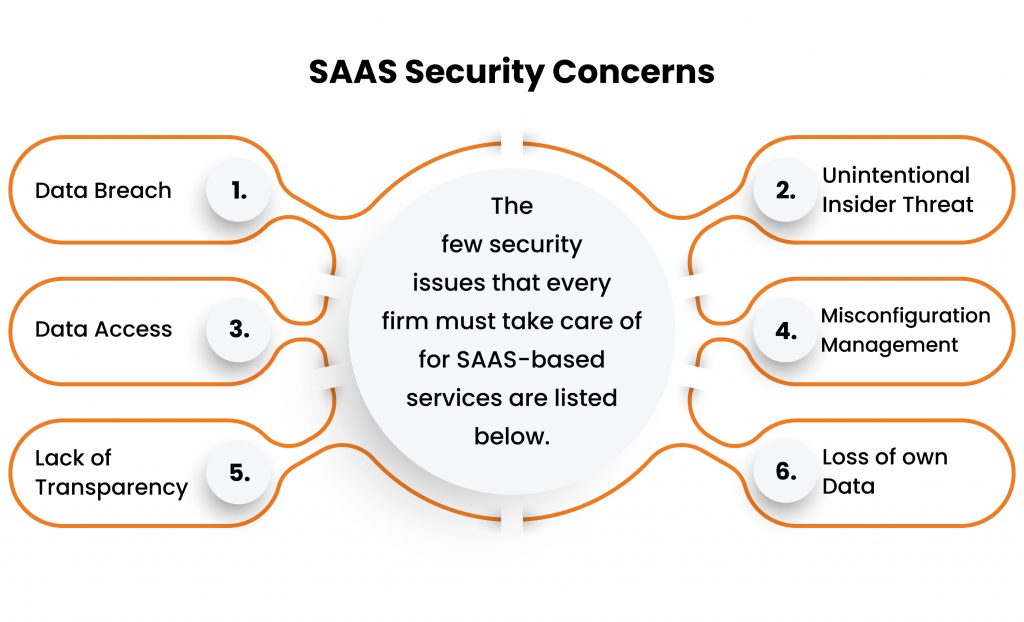
1. Data Breach – Due to its numerous advantages—which include no initial setup fees, simple upgrades, quick implementation, and many more -data will constantly take the lead. Your personal information could potentially be accessed by someone. Be prepared for lawsuits and brand damage if the vital data assets are owned by another business. Cybercriminals utilize sophisticated techniques including phishing, ransomware attacks, virus exfiltration, and more to access, recover from, or adversely damage sensitive data.
A recent security breach involved Mailchimp, the most popular SaaS-based service provider, where an attacker breached Mailchimp and gained access to Digital Ocean customers’ accounts.
2. Unintentional Insider Threat – One of the biggest hazards to businesses, according to many accounts, is insider assaults. Sometimes they’re intentional (when a disgruntled employee seeks to directly harm the business), but most of the time they’re just the outcome of an honest mistake or negligence (for instance, losing data by sending an email to the incorrect address, losing external storage devices, smartphones, and laptops, or doing something similar).
Research revealed that only 23% of all instances had insiders as the source, and of that 23%, 61% were the consequence of data handling errors. There have been 54 breaches proved to be caused by insiders in all, some of which were rather painless for the business and others which were downright horrific.
3. Data Access –Data storage is located in a remote area and is disguised. It follows that there are servers out there that are keeping and protecting your sensitive data because the ability to restore data is given. Discovering who else has access to the data is similarly important.
On August 4, 2022, Twilio an American-based programmable communication tool company discovered that a sophisticated social engineering scheme designed to steal employee credentials had given unauthorized access to information related to a small number of Twilio customer accounts. As a result of this extensive assault on the personnel base, several employees were tricked into providing their credentials.
4. Misconfiguration Management – The assigned level of configuration needs to be monitored carefully. A permission gap may emerge if an administrator grants end users access rights or permissions too frequently. The risk of cloud data being exposed to faults that could lead to leaks and breaches is increased by the growing authorization gap. One of the easier setup errors for hostile actors to take advantage of is the boot disc volume, encryption, and storage.
5. Lack of Transparency – SaaS providers usually uphold confidentiality. They convince their clients that they are more adept at protecting their private data. They also make sure that they can secure data and files more effectively than their clients can. However, this lack of transparency could irritate their clients. Both clients and industry experts frequently have queries about security that go unanswered. There are holes and conjectures in their understanding of the service they are using or reviewing.
6. Loss of own Data – The SaaS provider is in charge of managing the activities related to data storage. That can be reassuring, but it also implies a loss of some control, leaving customers open to worries and, regrettably, costing them time while they wait for solutions when problems arise. Benefits include not having to manage, update, or alter your cyber security. Despite this, there is a disadvantage in that we no longer have total control over our own data. Everything is dependent on the service’s degree of customization, which might only be modest in some instances.
How to Mitigate SaaS Security Concerns?
A major area of concentration should be SaaS security management and governance, which are essential for an enterprise’s cyber defense. For the proper application and definition of security controls, data, and identity protection, as well as application monitoring, are crucial. Below we will discuss a few areas in which we can mitigate such concerns –
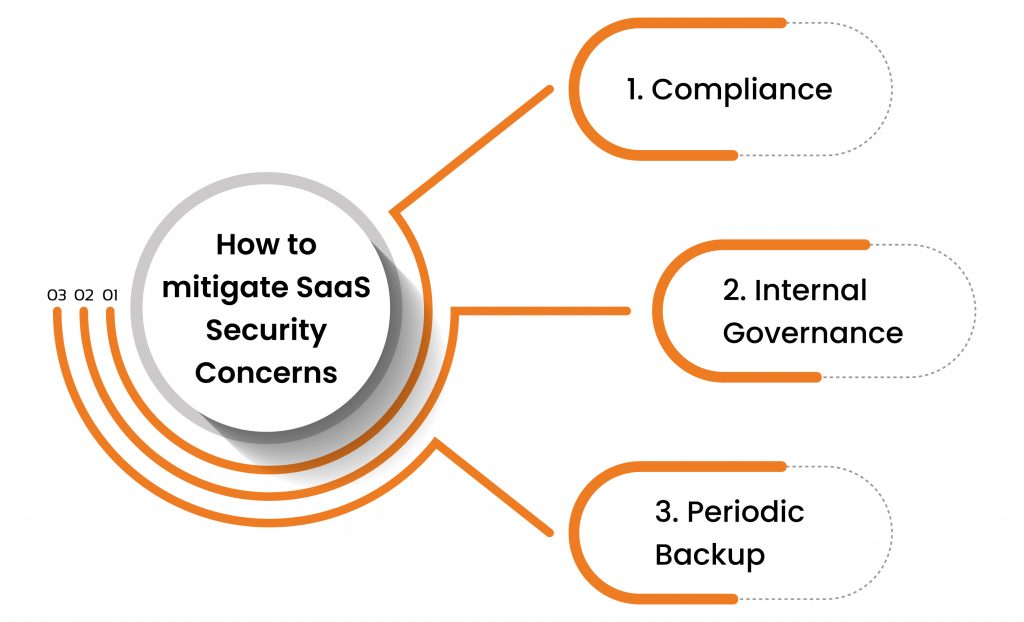
1. Compliance – Organizations should adhere to security regulations like GDPR, HIPAA, and PCI DSS since they have a direct impact on the quality of the services provided. Utilize internal audits to verify that regulations, such as IS0 27001, are being followed. To win the trust of your clients, you might need to demonstrate your comprehensive compliance and data protection through tools, procedures, and skills.
2. Internal Governance – The highest security layers can be enforced on-site, but many employees might not be as secure, despite the fact that remote work is frequently employed in many places. In many circumstances, the fact that businesses don’t control the technology being used just makes the problem worse. With more endpoints in dangerous locations, security breaches are more likely to occur. Giving each resource a business laptop that comes pre-installed with security tools like login authentication, VPN blocking, regular backups, etc. is the best method to combat this.
3. Periodic Backup – Operations won’t be interfered with, and a sufficient backup will protect the server. This lets you maintain business operations while making sure that the security team of your SaaS vendor can take prompt remedial action to halt any data theft in its tracks and prevent further abuse of sensitive data.
Conclusion
SaaS solutions are far from impervious, and they may cause significant cybersecurity issues. Even if it might be argued that users are generally not responsible for keeping them secure, it is crucial to point out that they are nonetheless vulnerable to various types of cyberattacks. To prevent giving bad actors the chance to deploy harmful software or identify weaknesses in the SaaS systems they are utilizing, organizations must take sensible security precautions.
We are a CERT-In empanelled organization with teams of developers, testers, and quality assurance experts who are skilled at building reliable and secure mobile applications. With the help of our automatic and human VAPT services, which find, identify, and evaluate the vulnerabilities inherent in your IT framework, Kratikal can help you become more aware of these risks. To assist your company in addressing security issues brought on by SAAS-based services, we also provide security auditing for Compliance, including ISO/IEC 27001, GDPR, PCI DSS, and many more.
Although cyber security issues in SaaS-based services are a common topic, many firms still choose to ignore them. Do you believe these security issues might be prevented if preparations were taken in advance? Share your ideas in the comments below!








Leave a comment
Your email address will not be published. Required fields are marked *