The internet that we use today is a massive network of interconnected devices and services. Application Programming Interfaces (APIs) are an essential but sometimes invisible technology layer that underpins services ranging from social media to online banking. APIs serve as messengers between apps, allowing them to communicate data and functionality seamlessly, making API security a top priority.
A recent article reveals a surprising fact: APIs drive the vast majority of Internet traffic. This may frighten many users who usually interact with the internet via web browsers. However, beneath the surface of user-friendly interfaces, a complicated web of API calls enables the flawless operation of numerous online activities.
Table of Contents
Role of API Security: A Closer Look at Its Seamless Communication
Assume you wish to order some good food for yourself on a Sunday morning through a cafe’s website. You explore the menu, select your food choices, and place the order. This seemingly easy process is the result of several APIs working together. When you click the “Add to Cart” button, the website sends an API request to the cafe’s inventory management system. This API detects item availability and updates the cart total.
Similarly, when you go to the checkout, another API request goes to a secure payment gateway to process your credit card details. Finally, after successful payment, an API sends the order details to the cafe’s kitchen management system, which begins meal preparation.
This example shows how APIs serve as mediators. It allows various apps to securely communicate and share data. They develop a set of regulations and standards that govern how apps interact with one another. This standardization allows seamless communication. This is done regardless of the programming languages or underlying technology utilized by the applications.
API Vulnerabilities: A Prime Target for Hackers
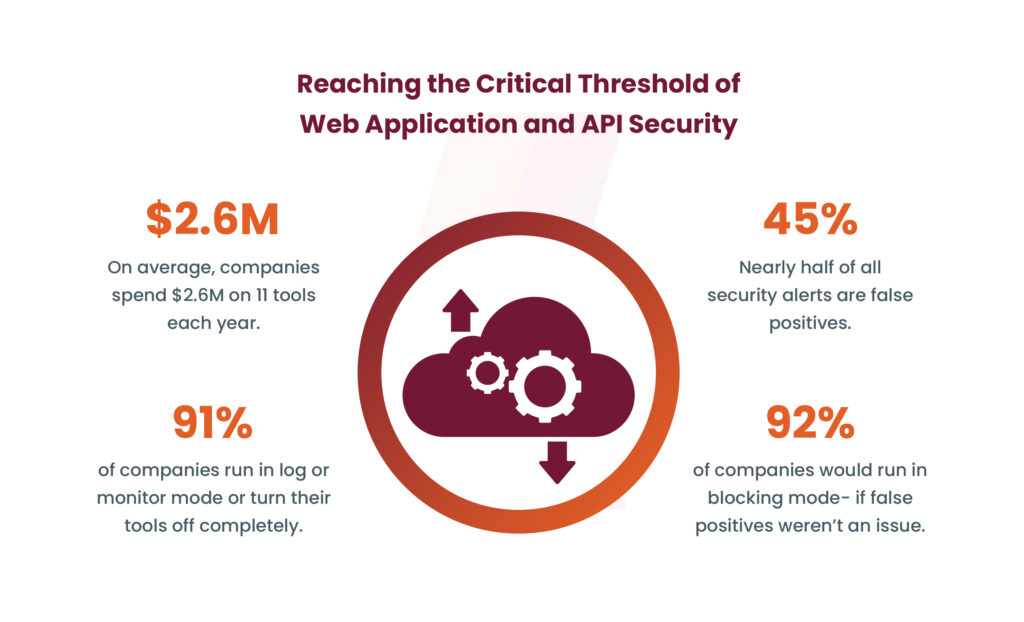
Despite their importance, APIs are also becoming a prime target for hackers. Recent reports suggest that approximately 71% of websites worldwide are vulnerable to API security breaches. Hackers exploit these vulnerabilities to gain unauthorized access to sensitive data, manipulate systems, or launch other malicious activities.
Book Your Free Cybersecurity Consultation Today!
One of the primary reasons behind this vulnerability is the rapid growth of APIs without adequate security measures. As businesses rush to develop new digital services and integrate with third-party platforms, they often overlook the importance of robust API security protocols. Additionally, APIs are often designed to be accessible and flexible, which can inadvertently create security loopholes if not properly secured.
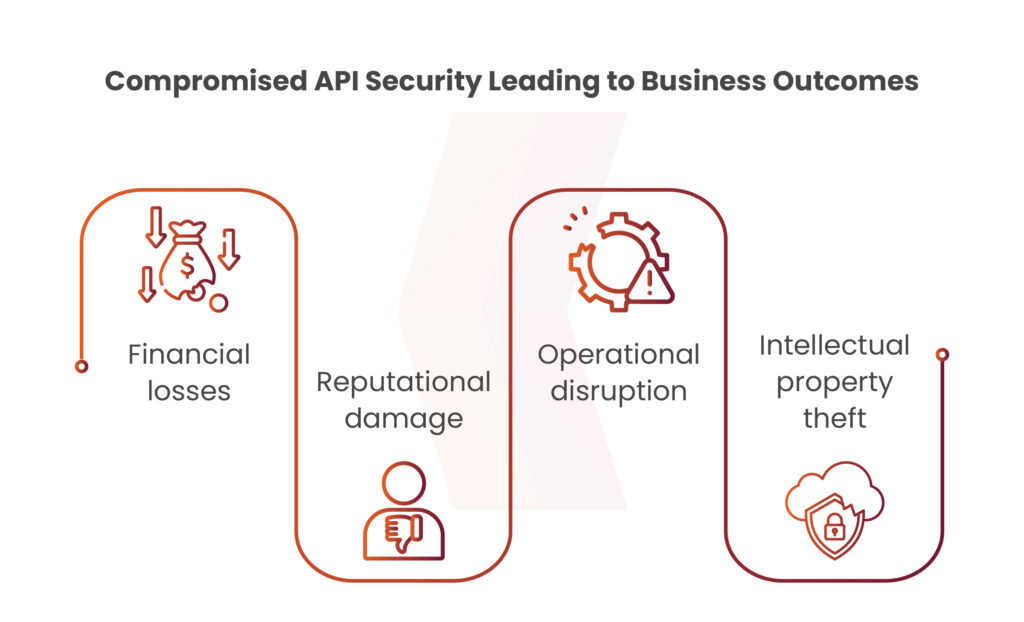
The consequences of API security breaches can be severe. From financial losses due to data theft to reputational damage and regulatory penalties, organizations face significant risks if their APIs are compromised. Moreover, with the increasing adoption of cloud computing and mobile technologies, the attack surface for API vulnerabilities continues to expand, making proactive security measures more critical than ever.
Mismanaged API Security as a Serious Threat for Your Business
Mismanaged APIs pose a significant security threat to organizations, manifesting in various forms such as shadow, deprecated, and unauthenticated APIs. Shadow APIs, which are often undocumented and outside the purview of security teams, can grant unauthorized access to sensitive data. Deprecated APIs, if not properly updated or removed, become vulnerable endpoints lacking the necessary security patches. Unauthenticated APIs, typically resulting from misconfigurations or rushed releases, expose organizations to the risk of data breaches and unauthorized access. These vulnerabilities highlight the critical need for robust API management and security measures.
Securing APIs: Best Practices and Solutions
Securing APIs: Best Practices and Solutions
To reduce the risks of API security breaches, businesses must take a proactive approach to API security. This involves putting in strong authentication and authorization procedures, encrypting sensitive data in transit and at rest, and periodically monitoring and auditing API traffic for suspicious behavior.
Get in!
Join our weekly newsletter and stay updated
Furthermore, organizations should prioritize API security awareness programs for their development teams to ensure that they understand the value of secure coding methods and follow industry best practices for API security. Using advanced API security solutions like API gateways, web application firewalls, and API management platforms can provide levels of defense against common API vulnerabilities including SQL injection attacks, broken authentication, and excessive data exposure.
Conclusion
In an era where APIs generate the bulk of internet traffic and 71% of websites are exposed to API security breaches, protecting APIs has become critical in the domain of cybersecurity. Vulnerability Assessment and Penetration Testing (VAPT) techniques are critical for discovering and fixing potential problems in API implementations. Kratikal, being a CERT-In empanelled auditor helps with managing API vulnerabilities and reduce the chances of cyber attacks. Organizations can reduce the risk of API security breaches by employing proactive security measures such as strong authentication, encryption, and regular monitoring with guidance of best cybersecurity company. They not only protect sensitive data and systems but also maintain their reputation and regulatory compliance in today’s linked digital landscape.
Reference Source: https://thehackernews.com/
Watch this video now and learn more about why API Security matters!
FAQ
- What are APIs, and why are they important?
APIs, or Application Programming Interfaces, are software intermediaries that allow different applications to communicate and share data seamlessly. They are essential in enabling the integration of various digital services and facilitating the smooth operation of online activities.
- Why is API security important for businesses?
API security is crucial for businesses since APIs often serve as gateways to sensitive data and critical systems. Without adequate security measures, APIs can be vulnerable to various cyber threats, including data breaches, unauthorized access, and manipulation by malicious actors. Protecting APIs is essential for safeguarding sensitive information and maintaining the trust of users and stakeholders.








Leave a comment
Your email address will not be published. Required fields are marked *