Ransomware attacks since the past 15 years have taken a drastic transformation in terms of its intensity. The first ever Ransomware attack reported in the history was deployed via floppy disks back in 1989. It was popularly known as the AIDS Trojan. Though it may sound really quaint, but in a way, this older version was considered even more deceitful than its present descendants. Modern versions lure victims using legitimate-looking e-mail attachments, which can consist of a fake invoice or a fake receipt. But back then, in the early 90’s, dispatching 20,000 disks across 90 countries was disguising something that was far more severe. But it wasn’t until the global havoc caused by WannaCry in 2017 that Ransomware entered the public consciousness.
In 2017, Ransomware has been an eminent threat in the cybersecurity landscape. Large as well as small enterprises shelled out millions of dollars in order to retrieve their encrypted data. Between the year 2005 and 2016, more than 7600 Ransomware cases were received by the Internet Crime Complaint Centre (IC3). However, these numbers cannot be considered precise as the real scenario is way more brutal.
According to Kaspersky, there has been an increase in the number of corporate users who have fallen victim to crypto-ransomware. Most of these attacks were targeted to small and medium-sized businesses, although earlier, attacks were typically spread across individuals – which still involve the majority of attacks today.
Throughout the years, ransomware has grown from a curiosity and a worry to a major crisis, circumvolving deeply with top spy agencies and international conspiracy. Some of the worst ransomware attacks that almost shook the world are listed below:
1. NotPetya
This particular Ransomware attack affected hundreds of thousands of computer systems across 100 countries over a short span of time. Initially, it was stated as a fake Ukrainian Tax software update and was responsible for compromising a number of firms in the US, causing major financial damage. Pharmaceutical giant Merck was held under this attack which resulted in a financial loss of more than $300 million!

Source: securityintelligence.com
2. WannaCry
Considered as one of the most devastating ransomware attacks in the history, it was responsible for affecting several of hundred thousand machines and crippling banks, law enforcement agencies, and other infrastructure entities. In May 2017, within a period of 4 days after the attack was deployed, there were almost 250,000 detections across 116 countries. It was also reported that hospitals in Ukraine and radio stations in California were also shut down.

Source: komando.com
3.CrySis
Started in the year 2016 across Australia and New Zealand, this particular attack was spread by hacking into Remote Desktop Services and manually installing the ransomware into the systems. It is considered as the most common way to deploy a ransomware, as the attackers can compromise administrators and devices that can control the entire organization. It was reported that around 200 master keys were released, which allowed the victims to decrypt and unlock their systems.

Source: bestsecuritysearch.com
4.Cryptomix
In this type of attack, the attackers do not have any portal on the dark web for initiating ransom. Instead, the victims are told to wait until the cybercriminals who took their systems as a hostage, gave them instructions for the payment of Bitcoins via e-mail.
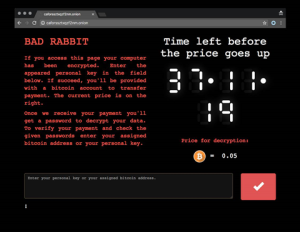
5.BadRabbit
This particular ransomware was seen active in parts of Ukraine and Russia, the victims included Russian news media outlets Fontanka.ru and Interfax, as well as Kiev’s metro system and an airport in Odessa. Unlike attacks like WannaCry and NotPetya, it used drive-by attacks to deliver the ransomware dropper. This attack was responsible for Targeting only hundreds of victims, demanding a ransom of 0.5 bitcoins.
Source: itnews.com
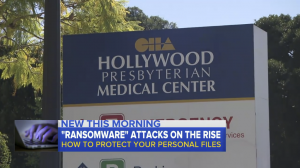
6. In the year 2016, a Los Angeles hospital system, Hollywood Presbyterian Medical Center (HPMC) was held under a ransomware attack. Attackers allegedly demanded a ransom of around $3.4 million. The attack forced the hospital back into pen and paper era, blocking access to the company’s network, email, and crucial patient data for ten days.
Source: pcantivirusreviews
7. Emory Healthcare, an Atlanta healthcare system has been hit with a data breach and a ransomware attack that affected the electronic health records of nearly 80,000 The compromised records which contained appointment information included data like; patient names, contact information, medical record numbers, service dates and even the names of the physicians.
8. Guests at the Romantik See hotel Jaegerwirt in the Austrian village of Turracherhohe were locked outside their rooms. The criminals had disabled the electronic key system until a ransom fee was paid to them. Also, the computers were held hostage which restricted the hotel staff to issue new key cards. In total, the hotel paid a ransom of around €1,500 (£1,275) worth of bitcoins.

9. Texas police in the town of Cockrell Hill has reportedly lost eight years’ worth of digital evidence after getting hit by a ransomware attack in December 2016. The malware came from a spam email that had come from a cloned email address impersonating a department-issued email address. The attack resulted in the loss of all bodycam video, photos, in-car footage, and some police department surveillance videos as well.
10. In 2015, a ransomware variety known as TeslaCrypt or Alpha Crypt hit 163 victims, netting $76,522 for the attackers behind it. TeslaCrypt demanded ransoms by Bitcoin, or in some cases PayPal or My Cash cards, in amounts ranging from $150, to as much as $1,000.
Future of Ransomware Attacks..
Progressively, the attacks are getting more creative in monetizing their efforts, with Petya ransomware pioneering ransomware-as-a-service last year. Also, the source of the code doesn’t really matter for the victims, whether you’re infected with Petya or any other malware, the end result is the same. Quite recently, authors of the Saturn Ransomware rolled out RaaS program which allowed wannabe ransomware distributors to earn as much as 70% of the ransom via affiliate schemes.
What’s next for ransomware?
A new report from the National Cyber Security Centre (NCSC) and National Crime Agency, UK (NCA) have given warning against developing threats such as ransomware-as-a-service and mobile ransomware in the coming years. It has also predicted that these attacks pivot to target connected devices such as smart TVs and fitness trackers.
Household held under ransomware attacks
The proliferation of IoT and digitization into our day to day life, everyone and everything will become a potential target in the coming future. Introducing IoT into general household goods such as watches, mobile devices, television, kitchen appliances etc. will possibly put 10s of billions of devices into an attack. The rate at which the technology is growing combined with the widely-reported insecurity of IoT devices, it is masquerading towards a whole new frontier for ransomware operators.
Transportation hacks
Hacking a vehicle can be the most devastating event that can occur under the influence of a ransomware attack. Smart cars have a high potential of getting remotely controlled by an attacker sitting in any part of the world. We are just a few years away to witness autonomous trucks and cars and there are already instances reported where external actors are taking control of the vehicles.

Source: virusremovalinstructions
Hacking a vehicle can be the most devastating event that can occur under the influence of a ransomware attack. Smart cars have a high potential of getting remotely controlled by an attacker sitting in any part of the world. We are just a few years away to witness autonomous trucks and cars and there are already instances reported where external actors are taking control of the vehicles.
Outage in factory lines
The introduction of AI has been replacing the factory workforce significantly. Companies like Honda, NHS, and FedEx are among the victims in the WannaCry outbreak. Honda has to terminate the production of around 1000 cars after the Japanese plant was hit by ransomware. Soon such companies will work on automated and computerized workforces which can largely aid in infiltrating ransomware attacks.

Despite incorporating best security practices, many individuals still fail to regularly back up their data. Some enterprises do so only within their own networks, which also depicts that duplicate backups too can be compromised by a single ransomware attack. Ransomware defense ultimately depends on effective education. Awareness simulation tools like Threatcop provides a great platform for the risk assessment of the workforce of an organization, providing a real-time threat analysis report of the people of an organization. It is carried out by deploying simulated cyber attacks like ransomware, phishing, smishing, etc. in an incognito environment.
Users, employees as well as businesses should invest time to learn about the best options for automated data backups and software updates. Also, awareness about the ransomware attacks, such as phishing attacks, compromised business emails that are drive-by downloads, malicious attachments, and spoofed websites, should be a top priority for anyone using an internet-enabled device in today’s digital era.








Leave a comment
Your email address will not be published. Required fields are marked *