Zero-day exploits have set a trend recently with their growing reported cases coming into the light. Even though there is a significant acceleration in vendors fixing the security vulnerabilities in the last 2 years, according to a report from hitechglitz, the hackers, too, it seems, have become quicker at detecting those vulnerabilities and exploiting them.
One of them is especially tormenting Google’s Chrome, which has currently been infected by a ‘high-severity’ vulnerability that is being actively exploited in the wild.
The bug recorded as CVE-2022-1096 is a ‘Type-confusion’ error in an open-source engine, V8 JavaScript Engine used by Chrome and Chromium-based web browsers.
Some of the browsers that use Chrome’s open-source Chromium codebase include:
- Microsoft Edge
- Opera
- Vivaldi
- Comodo Dragon
- Brave
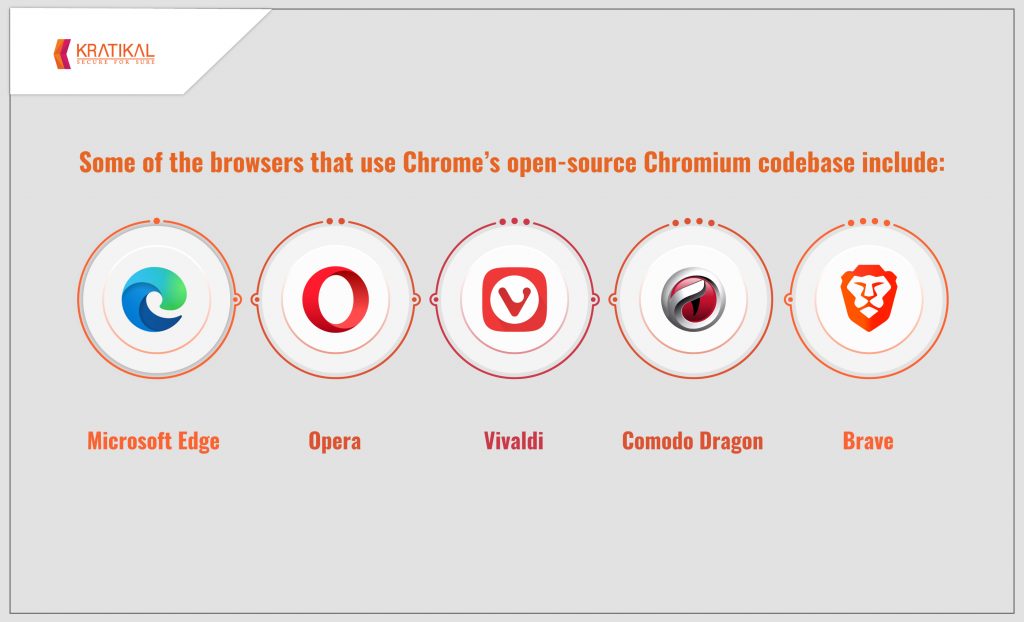
Table of Contents
CVE-2022-1096: A TYPE-CONFUSION ERROR
After patching up a severe Chromium Zero-Day flaw, CVE-2022-0609, in the Animation component on February 14, 2022, Google Chrome has yet again been hit by another vulnerability in its system. CVE-2022-1096, a ‘type-confusion’ issue has made Google come to a standstill.
As reported by an anonymous researcher on March 23, 2022, the vulnerability has been almost resolved by bringing forth an update to mitigate all the potential threats. Google acknowledged its awareness of the existence of an exploit for CVE-2022-1096 in the wild and advised its users to update to the latest version.
Type-confusion vulnerability
A Type-confusion error occurs when an object is passed to the code without the program verifying it first. The code then uses that information without type-checking it, which leads to type confusion.
It is especially dangerous because it leads to out-of-bounds access in languages that are not memory safe, like C and C++. Also, the wrong function pointers or data that is being put into the wrong piece of code can, in some cases, lead to a crash, or possible code execution.
WHAT ARE ZERO-DAY VULNERABILITIES?
Zero-day vulnerabilities refer to the newly discovered flaws in the system that are unpatched, leaving them defenseless to social engineering attacks. It is called ‘zero-day’ because it is discovered first by the attackers before any security analyst can detect it.
These undetected loopholes in the system can jeopardize the networks or the operations of an enterprise, making them a severe security threat.
The attacks typically come in the form of malware which is released in the unpatched vulnerability in a web browser or an application. The malware, which is sent via email, is injected into the system by clicking on suspicious links or downloading the infected attachment in the email.
The Zero-day exploit can result in confidential data theft, corruption of critical files, taking control of the devices, and many more. Data leakage prevention plans can help solve this issue.
Some related terms to understand Zero-day vulnerabilities:
- Zero-day exploits – The social engineering methods to execute attacks.
- Zero-day attacks – The attacks that take advantage of the vulnerabilities to cause data breaches in an organization.
HOW ZERO-DAY ATTACKS ARE CARRIED OUT
Software developed in a company contains a vulnerability that the developer isn’t aware of — The threat actors spot it and act upon it before it is discovered by the developer — Methods to exploit it are then executed while it remains unpatched — a successful Zero-day exploit — Noticed by someone in the form of data theft — The developer creates a patch for it.
SOME FAMOUS ZERO-DAY EXPLOITS –
- AURORA – A series of cyberattacks launched from China that targeted U.S. private sector companies in 2010. A phishing campaign was launched by threat actors to steal trade secrets of Yahoo, Adobe, Morgan Stanley, Google, and more than two dozen companies that compromised their networks.
- ALIBABA – For 8 months, Alibaba’s shopping website was taken over by a web-crawling software developed by an unnamed developer in November 2019 to collect over 1.1 billion pieces of user information, like user IDs, mobile phone numbers, and customer comments.
- STUXNET – A computer virus attack that was suspected to have been led by the U.S. and Israeli governments to keep Iran from making nuclear weapons. It is considered the first world’s cyber weapon.

WAYS TO TACKLE A ZERO-DAY ATTACK –
The best way to prevent any cyberattack from happening in the first place is the maintenance of a good firewall and an up-to-date antivirus. It ensures the server security.
- A Web Application Firewall (WAP) is the first line of defense in network security. It forms a barrier between the trusted internal network and the outside network, like the internet. Inspecting incoming and outgoing traffic can identify and block threats.
- IT security assessment plays a major role in securing the networks as well. Network Security Testing can help improve the overall security of your networks by :
- Constantly Identify the threats to the networks.
- Checking for security access control.
- Analyzing network-based intrusions.
- Applying patches as soon as they become available to fix the vulnerabilities. They can also help fix previous vulnerabilities by providing updated software.
Also, since Zero-day vulnerabilities are intimidating enough to be considered a high-priority threat, performing regular VAPT can help. VAPT thoroughly analyzes a network to detect all the exploitable vulnerabilities present in it. It is a foolproof way to guarantee the safety of your organization’s IT infrastructure.
CYBERSAFETY WITH KRATIKAL
As a CERT-In empanelled company, Kratikal firmly hopes for a world free of cybercrime. For the safety of your systems, we offer the complete suite of Vulnerability Assessment and Penetration Testing (VAPT) services such as Web Application Security Testing, Network Security Testing, Medical Security testing, and many more. These testing services identify all the security vulnerabilities in a system to shield them from possible social engineering attacks.
As a new day rolls in, so does the report of a new Zero-day Vulnerability attack. It has become an issue important enough to warrant complete attention of both the vendors and the hackers.
Vulnerabilities in a system are inevitable but don’t lose heart.
Where there is a problem, there is always a solution hidden under there, somewhere!
What do you suggest to tackle Zero-day vulnerabilities? Comment down below!








Leave a comment
Your email address will not be published. Required fields are marked *