The news of a new Zero-day Vulnerability has the internet buzzing. With its high criticality threat level, Spring4Shell, or Spring Shell, is keeping software suppliers awake at night. Because of its widespread use in Java applications, Spring4Shell, with its CVSS score of 9.8, is already being compared to Log4J Shell.
According to a report by Info security-magazine, the vulnerability has triggered exploitation attempts in over 16 percent of businesses worldwide, with Europe being the most affected country (20%) and the software industry being the most afflicted service (28 percent).
During the first four days after its release, 37 thousand attempts to exploit the Spring4Shell vulnerability were made all around the world.
Table of Contents
What is Spring4Shell (aka Spring Shell)?
Spring4Shell is a critical vulnerability found in the core of Spring Java Framework, a programming configuration model providing infrastructure support for developers building Java applications, which is part of the Java Development Kit (JDK) versions 9.0 and later.
Researchers weren’t sure if this was a Zero-day vulnerability or a previous error in the Spring Java Framework, but it turned out to be something completely different. The code CVE-2022-22965 was then allocated, indicating that it was a critical vulnerability.
The Remote Code Execution (RCE) Vulnerability can be easily exploited by sending a specially crafted HTTP request to a server running the Spring Core Framework. Cisco and VMware are currently being exploited by this RCE bug.
The affected Cisco products are:
- Cisco Crosswork Optimization Engine
- Cisco Cosswork Zero Touch Provisioning (ZTP)
- Cisco Edge Intelligence
The affected VMware products are:
- VMware Tanzu Application Service for VMs (Versions 2.8 through 2.13)
- VMware Tanzu Operations Manager (Versions 2.8 to 2.10)
- VMware Tanzu Kubernetes Grid Integrated Edition (TKGI) (Versions 1.12 and 1.13)
The patches for VMware Tanzu Application Service for VMs and VMware Tanzu Operations Manager are available, but the patch for VMware TKGI Edition is still pending.
Remote Code Execution (RCE) Vulnerability
A Remote Code Execution or Arbitrary Code execution is a vulnerability in web applications where an attacker exploits a server possessing the weakness by running a code of their own choice with system-level privileges. The attacker is able to exclusively command the affected person’s computing device or system.
An RCE attack takes place when the host downloads malicious malware, and can strike a person regardless of the current location of their device or system. The aftermath of the attack can range from malware execution to overall access control over the compromised system.
An attacker can execute an RCE attack by using:-
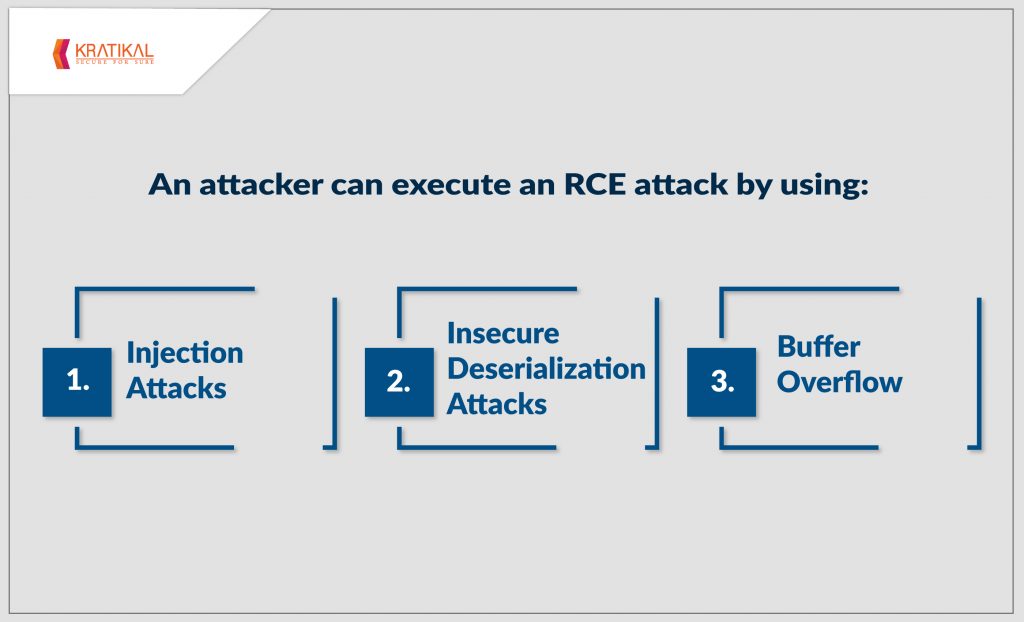
- Injection Attacks
Injection attacks occur when an attacker inserts (or injects) their own code into a program. Since the program is unable to determine the injected code on its own, attackers are able to gain easy access to the confidential data stored in the systems. Some of the most famous injection attacks include:
- SQL Injections
- Command Injections
- CRLF Injections
- LDAP Injections
- Insecure Deserialization Attacks
A major threat with serious consequences, Insecure Deserialization occurs when a malicious object is inserted into a web application which leads to the infliction of Denial-of-Service (DoS) attacks, Remote Code Execution attacks, SQL Injection attacks, Authentication Bypass, and many more. It is ranked 8th number in the OWASP Top Ten List of the most critical web application vulnerabilities.
- Buffer Overflow
Buffer overflow attacks usually corrupt a web application or a server by sending a carefully crafted message to a web application or server to execute arbitrary code and effectively take over a machine. It can generally lead to crashes.
Some High-severity Remote Code Execution Attacks –
- CVE-2021-44228, Log4Shell
The highly critical Remote Code Execution vulnerability with a CVSS score of 10.0 wreaked havoc in the popular library in Java code, Log4j, developed by Apache Software Foundation back in December 2021. It affected the 2.0 and higher versions of the Log4j library. The attackers executed this to install cryptocurrency miners, Cobalt Strike, and to recruit devices into a botnet.
- CVE-2017-0143, Windows SMB RCE Vulnerability (WannaCry)
In a global epidemic attack in May 2017, WannaCry targeted Microsoft Windows users by encrypting their data and demanding a ransom in the form of a bitcoin. It was executed by exploiting a vulnerability in Microsoft Windows operating systems using a hack called “EternalBlue”, allegedly developed by the United States National Security Agency.
What Can We Do to Prevent a Zero-Day Vulnerability?
The threat posed by Zero-Day Vulnerabilities cannot be ignored. They have become special targets for threat actors due to their hidden existence. The vendors not being aware of the vulnerabilities make them defenseless against cyber attacks.
While the Spring4Shell can only be exploited if a number of conditions are met, it is still a high-severity threat. To deal with it accordingly, an official patch has been issued by the Spring team to mitigate the threat. Users are advised to update to the newer versions to avoid further exploitation.
For almost every Zero-day Vulnerability, patches are issued as quickly as the vendors become aware of the loophole, but should you really be waiting for a patch? Who knows how much data can be compromised in that short period if your system gets compromised?
There are some crucial measures that are needed to be taken to eliminate the threat of Zero-day Vulnerabilities, including: –
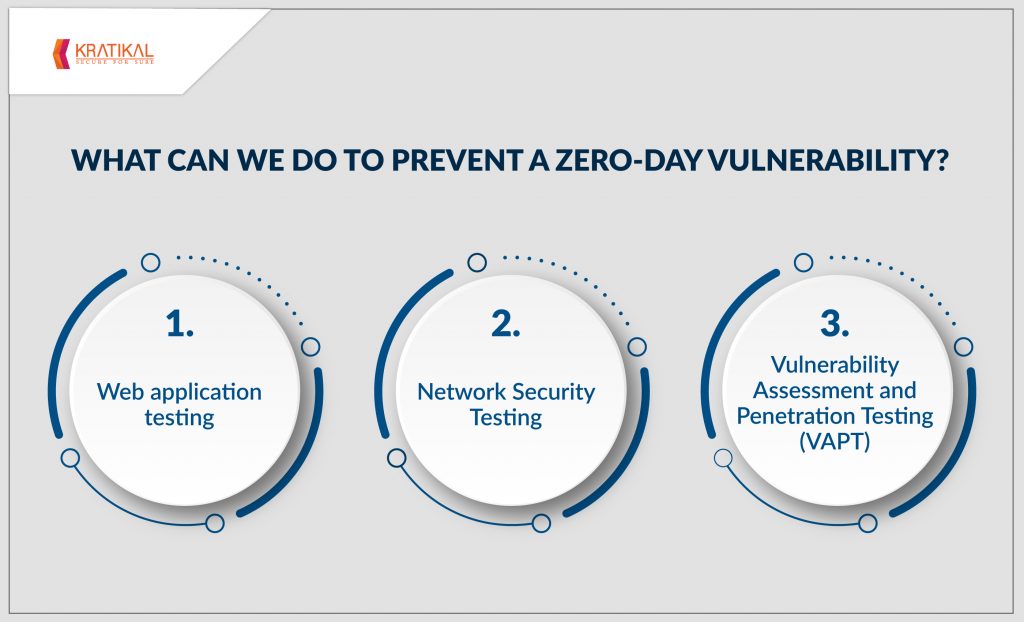
- Web application testing
Application Security Testing is a reliable way to detect all the vulnerabilities present in your Web and Mobile applications infrastructure and online services. It detects all the most vulnerable aspects present in the applications to ensure their protection against Zero-day attacks.
- Network Security Testing
Infrastructure Penetration Testing can evaluate the state of both the internal and external network to detect all the exploitable vulnerabilities in networks, network devices, systems, and hosts so they can be patched before a hacker can discover and exploit them.
- Vulnerability Assessment and Penetration Testing (VAPT)
Performing regular VAPT is the most certain method of eliminating all the vulnerabilities present in your networks and devices. VAPT runs an in-depth analysis of a program to expose all the exploitable vulnerabilities present in them. It is an effective measure to secure all your networks.
How Can Kratikal Help?
Kratikal Tech Pvt. Ltd. is a software consultancy firm dedicated to making the world free of social engineering attacks. As a CERT-In empanelled company, we offer a complete suite of VAPT testing services, including Web Application Testing, Network Security Testing, Cloud Penetration Testing, and many more.
Another day, another Zero-day exploit! A new day, however, brings with it a new opportunity to think about cybersecurity.
A fresh day gives you an opportunity to test your networks to ensure they can withstand a cyber attack!
Do you think Zero-day Vulnerabilities will ever stop tormenting us? Comment below and share your thoughts! Leave your opinion in the comments section below!









Leave a comment
Your email address will not be published. Required fields are marked *