
Table of Content
A Brief on Ransomware Attack
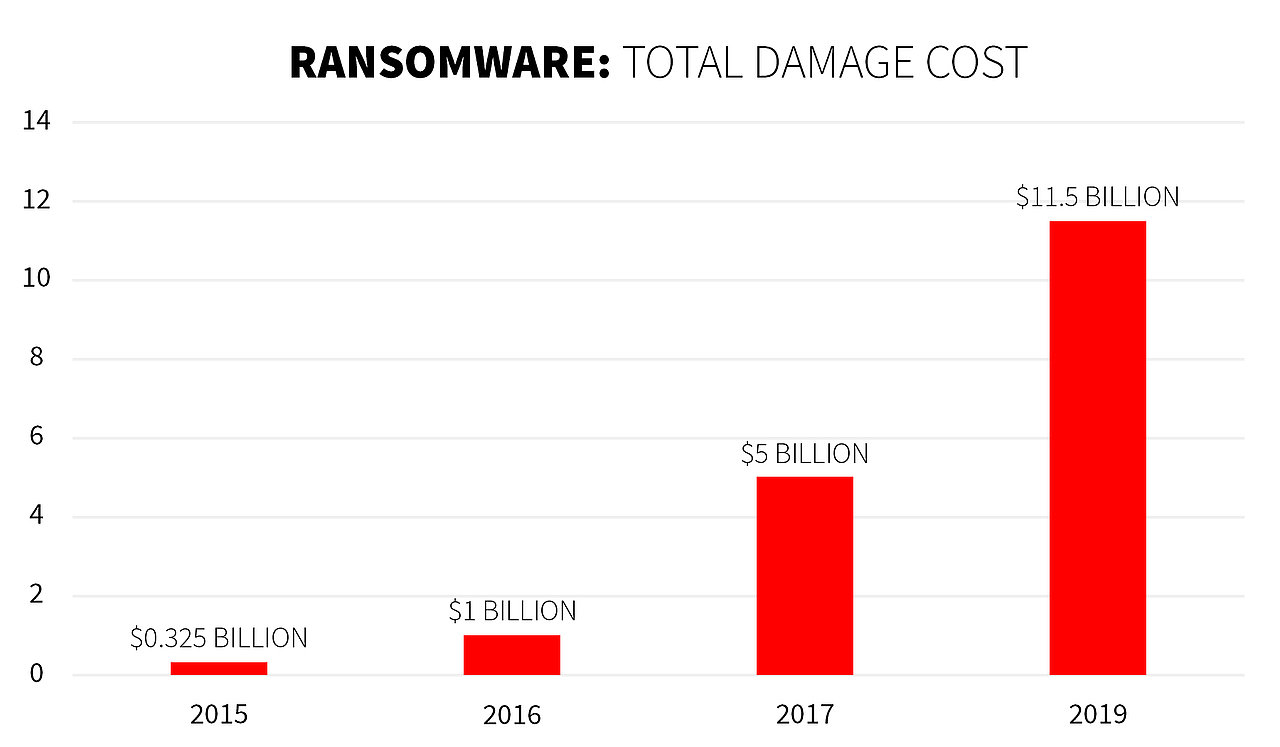
Ransomware has become a huge potential to exploit and damage users’ crucial data. This malicious attack was the most significant malware threat of 2018 and it continues to be the most dangerous even in 2019. With its growing popularity, more people are being targeted to get the ransom
Ransomware is malicious software that is designed to block user’s access to its computer or its important data by encrypting it. The vicious intent behind this attack is to get victims to pay a demanded ransom in return for the data.
In most cases, the ransom demanded from the victim comes with a deadline. If the victim fails to pay within the provided timeline, the data is lost forever. Ransomware attacks are very common these days.
Even paramount companies in North America and Europe have fallen victim to this malicious attack. Cybercriminals spare no one and can attack any consumer or business, coming from all kinds of industries. Various government agencies advise people against paying the demanded ransom as this might stop the ongoing cycle of ransomware attacks.
As a matter of fact, a ransomware attack is designed to extort money from victims by blocking access to their data or systems. There are two most prevailing types of ransomware attacks through which the attacks are deployed; encryptors and screen lockers.
Under encryptors, the index of data on a system is encrypted into absurd content and can only be restored with a decryption key. Whereas, screen lockers simply block access to the system by locking the screen, declaring that the system is encrypted. Apart from the two prevailing types, there are some infamous ransomware attacks as well.
Major Infamous Ransomware Attacks
-
Wannacry Ransomware Attack
This ransomware attack came out as a powerful Microsoft exploit. It was leveraged to create a global ransomware worm to infect over 250,000 computer systems. More than 200,000 systems were locked down in 150 countries. Hackers demanded a ransom which was paid through Bitcoin. Wannacry ransomware attacks infected National Health Service (NHS) and many other organizations across the globe.

-
CryptoLocker
It is a part of a ransomware family whose job is to extort money from users by encrypting the user’s hard drive as well as the attached network drives. It was the first among the current generation of ransomware that required cryptocurrency for a ransom payment. CryptoLocker was spread through an email attachment that claimed to have come from FedEx and UPS tracking notifications.
-
NotPetya
NotPetya is considered one of the most destructive ransomware attacks. It was coded in such a way that even if the user pays up the ransom, the data would still be unrecoverable. Infamous as a close relative of Petya malware, it successfully infected a thousand computers across the globe in 2017.
How to Prevent Ransomware Attacks
-
Ignore Unverified Links
Never click on links that come in spam emails or on any unfamiliar websites. If an unexpected download starts when clicked on a malicious link then there are high chances of your computer getting infected.
If you receive an email, call, or text from an untrusted source asking for your personal information, make sure you don’t give out the details. Cybercriminals trick users into getting their personal information in advance of an attack. They use your information to target you via a phishing email.
-
Backup your Data
If you ever experience a ransomware attack, you must already have a backup of your data so that you don’t have to pay any kind of ransom to the attacker. Make sure of keeping a copy of every important data in an external hard drive that is not connected to your system.
-
Never Pay Ransom
Never pay any amount to cybercriminals who carry out the ransomware attack. This is because there is no guarantee of return of data; after all your trust has already been manipulated with data hacking. Paying ransom only encourages cybercriminals to carry out more attacks.
-
Security Awareness For Employees
The best way to prevent a ransomware attack is by becoming proactive toward the latest cyber attack vectors. An organization must be aware of the harmful attack vectors which can lead them to the verge of losing their data and customer trust. It’s better to opt for preventive measures in advance so that there are fewer chances of falling victim to any kind of cyber attack.

Tools like ThreatCop come in handy for providing security awareness and analysis of threat posture in an organization. Humans can at times turn out to be the weakest link in the security chain of an organization. In order to turn them into the strongest link, Kratikal provides this exclusive tool for training individuals in the organization.
ThreatCop is a real-time threat posture assessment tool. It is a security attack simulator and awareness tool which analyzes the threat posture and helps individuals in the organization in improving their level of vulnerability towards cyber-attacks.
For Any query:
- Email: sales@kratikal.com
- Contact: India (+91) 7428797201, USA (+1) 323 287 9435


