Cyber threats are evolving at a pace that traditional security testing methods struggle to keep up with. Organizations today operate in highly complex digital environments with cloud platforms, APIs, microservices, and rapidly deployed applications. In such environments, manual security testing alone is no longer enough. This is where an AI pentesting tool becomes a critical component of modern cybersecurity strategies. AI-powered security testing platforms use machine learning, automation, and intelligent scanning techniques to detect vulnerabilities faster and more accurately than traditional approaches. These tools simulate real-world attacks, continuously analyze security weaknesses, and help security teams prioritize remediation efforts effectively. In this blog, we explore the best 5 AI pentesting tools in 2026 that organizations can use to strengthen their security posture and proactively identify vulnerabilities before attackers exploit them.
Table of Contents
Why Are AI Pentesting Tools Becoming Essential?
A traditional pentesting tool relies heavily on manual testing by security experts, which can be time-consuming and limited in scope. However, modern IT infrastructures require continuous monitoring and testing across multiple environments.
An AI pentesting tool offers several advantages:
- Automated vulnerability discovery across applications, APIs, and networks
- Continuous testing rather than periodic assessments
- Intelligent prioritization of vulnerabilities based on risk levels
- Faster detection of emerging attack patterns
- Reduced workload for security teams
With organizations adopting DevOps and cloud-native architectures, AI-driven pentesting platforms have become essential for maintaining strong security defenses.
5 Best Pentesting Tools in 2026
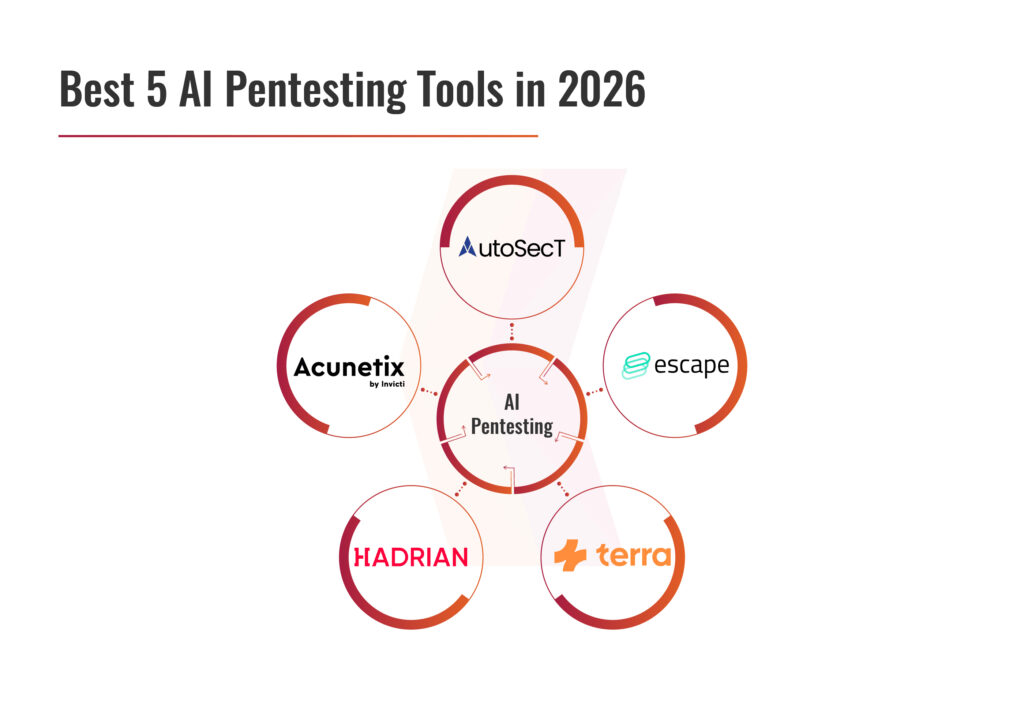
AutoSecT
Escape
Terra Security
Hadrian
Acunetix
AutoSecT
AutoSecT is a cutting-edge AI pentesting tool designed to keep your entire digital environment safe. It stands out by combining smart AI-powered vulnerability scanning and management along with pentesting, all from a single, easy-to-use dashboard. Whether you need to protect your network, cloud systems, web apps, mobile apps, or APIs, AutoSecT has you covered with tailored solutions that fit different industries and security needs. Its groundbreaking AI agentic Network Scanner, powered by advanced Retrieval-Augmented Generation (RAG), delivers precise and fast vulnerability detection, making network security smarter than ever before.
Comprehensive Security Coverage with Smart Automation
AutoSecT does not work with AI, but it is the AI in itself that automates vulnerability finding, allowing organizations to keep pace with the fast-evolving threat landscape. For your cloud environments, be it AWS, Azure, and GCP, the AI-driven pentest and VMDR platform performs real-time cloud monitoring that allows you to know your vulnerabilities from the very first scan itself. When scanning for network, AutoSecT, through its AI-agentic feature, generates appropriate AI-exploits to locate the flaws. The vulnerabilities are verified through AI, thus ensuring near-zero false positives. Through its AI-driven recommendation feature, it allows the security team to easily patch the vulnerabilities through the AutoSecT dashboard and collaborate across teams in real-time without the conventional chaos, apart from seamless integration with tools like Teams, Google Chat, bi-directional Jira, Slack, and Cliq.
Escape
The AI pentesting tool from Escape automates penetration testing using AI agents to continuously discover, test, and validate vulnerabilities in modern applications, APIs, and infrastructure. Instead of relying on periodic manual pentests, the platform performs ongoing security assessments, identifies complex business-logic flaws, and provides proof-of-exploitability with detailed remediation guidance. It integrates into developer workflows and CI/CD pipelines, helping security teams scale testing, reduce costs, and improve vulnerability detection across their environments.
Terra Security
Terra Security is a cybersecurity platform that provides an agentic platform for pentesting to help organizations identify and validate vulnerabilities across applications and infrastructure. The platform uses a swarm of specialized AI agents, supervised by human security experts, to simulate real attacker behavior and continuously test systems for exploitable weaknesses. By combining automation with human expertise, Terra delivers exploit-validated findings, continuous security validation, and actionable remediation guidance for modern development environments.
Hadrian
Hadrian’s agentic AI is designed to continuously identify exploitable vulnerabilities across an organization’s external attack surface. The platform autonomously discovers internet-facing assets, simulates real attacker behavior, and safely validates risks through controlled exploit attempts. Unlike traditional periodic assessments, this pentest tool performs continuous security testing, helping security teams quickly detect new exposures, prioritize critical vulnerabilities, and take faster remediation actions as environments evolve.
Acunetix
Acunetix is an automated web application security testing and pentest tool designed to detect vulnerabilities in websites, web applications, and APIs. It scans applications for thousands of security issues, including SQL injection, cross-site scripting (XSS), and other OWASP Top 10 risks. Using advanced crawling and proof-based scanning technologies, the platform identifies vulnerabilities, validates them with high accuracy, and provides actionable remediation guidance to help organizations strengthen their web security posture.
Get in!
Join our weekly newsletter and stay updated
How to Choose Right AI Pentesting Tool?
Selecting the right AI pentesting tool is a critical decision for organizations aiming to strengthen their cybersecurity posture. Modern enterprises operate in complex environments that include cloud infrastructure, web applications, APIs, mobile platforms, and distributed systems. Because of this complexity, choosing the right pentesting tool requires careful evaluation of several factors such as infrastructure coverage, automation capabilities, accuracy, and integration with development workflows. Below are some key factors organizations should consider when selecting the right tool.
- Coverage of Assets
One of the most important considerations when choosing a pentesting tool is the range of assets it can assess. Modern IT environments consist of multiple interconnected components, including web applications, APIs, cloud services, containers, and network infrastructure. A comprehensive AI pentesting tool should be capable of testing vulnerabilities across all these environments.
Security teams should ensure that the platform can identify weaknesses in web applications, API endpoints, databases, and cloud configurations. Additionally, the tool should be able to detect exposed services, misconfigured systems, and vulnerable software components across both internal and external environments.
- Automation Capabilities
Automation is one of the defining features of a modern AI pentesting tool. Traditional penetration testing often involves manual processes that can take weeks to complete and may only be performed periodically. However, cyber threats evolve rapidly, making continuous security testing essential.
An AI-powered pentesting tool should automate vulnerability scanning, attack simulation, and security validation processes. This allows organizations to perform regular security testing without placing excessive workload on internal security teams. It also enables organizations to test their systems whenever new code is deployed, infrastructure changes are made, or new applications are introduced.
- Accuracy and False Positives
Another key factor to consider when choosing an AI pentesting tool is the accuracy of its vulnerability detection capabilities. One of the common challenges with traditional scanning tools is the high number of false positives. A reliable pentesting tool should use advanced AI algorithms and validation techniques to confirm vulnerabilities before reporting them. This ensures that security teams focus only on real and exploitable threats rather than spending time investigating inaccurate alerts.
Book Your Free Cybersecurity Consultation Today!
Conclusion
Choosing the right AI pentesting tool is not just about finding a platform that detects vulnerabilities; it is about selecting a solution that aligns with the organization’s security strategy, infrastructure, and operational workflows. A well-designed pentesting tool should provide comprehensive asset coverage, intelligent automation, accurate vulnerability detection, seamless DevOps integration, and the scalability required to support growing digital ecosystems.
By carefully evaluating these factors, organizations can implement an AI-driven penetration testing solution that enables continuous security assessment, improves risk visibility, and helps protect critical systems from emerging cyber threats.
FAQs
- What types of vulnerabilities can AI pentesting tools detect?
Most pentesting tools can detect vulnerabilities such as SQL injection, cross-site scripting (XSS), authentication flaws, API security issues, misconfigurations, and other weaknesses across web applications, APIs, and infrastructure.
- How often should organizations use a pentesting tool?
Organizations should ideally run a pentesting tool continuously or regularly, especially after major code updates, infrastructure changes, or new application deployments.
- Is AI penetration testing suitable for small businesses?
Yes. Many modern pentesting tools are scalable and designed for organizations of all sizes. Small businesses can use AI-powered tools to automate security testing without requiring a large cybersecurity team.
- Are AI pentesting tools suitable for cloud environments?
Yes. Many advanced pentesting tools are designed to test cloud infrastructures, identify misconfigurations, and detect vulnerabilities across cloud platforms and services.









Leave a comment
Your email address will not be published. Required fields are marked *