In the last few years, Amazon S3 buckets have been linked to around 16 percent of cloud security breaches. (https://www.helpnetsecurity.com/2020/02/20/cloud-misconfigurations/). What are Amazon S3 buckets, and what can users do to avoid becoming the next headline?
In this blog article, we’ll go over the basics of Amazon S3 as well as several important security considerations for S3 customers.
Table of Contents
What is Amazon Simple Storage Services (Amazon S3)?
Amazon Web Services (AWS) defined as a service that provides object storage via a web interface to make web-scale computing more accessible to developers. This service enables companies of all sizes and industries to store vast amounts of data for a variety of uses, including websites, mobile apps, disaster recovery, and big data analytics.
What is an S3 Bucket?
Amazon S3, a popular object storage service with scalable storage infrastructure, launched in March 2006. S3, or Amazon Simple Storage Service, is a vital data repository for most businesses.
Developers increasingly rely on the flexibility and scalability of storing data in S3 to quickly construct apps. One of the most popular cloud storage solutions nowadays is Amazon Simple Storage Service (S3).
An Object cannot be self-contained; instead, it must be contained in a bucket. In one Amazon account, there are hundreds of buckets, each storing hundreds of products. S3 stores objects, which means that an application or a human can save a file in S3 just like they would in a regular file system.
Furthermore, each S3 item has a unique URL , accessed over the internet, making file distribution through the S3 service straightforward.
What are S3 severe security concerns?
- How affordable is the S3 Bucket? It is much less expensive to serve your website over S3 than it is to serve it from a server. As a result, more people choose the S3 bucket.
- You won’t have to worry about scaling as your traffic grows because there are no servers involved.
- There will be no downtime because of no servers. At all times, S3 buckets will be accessible.
Variety of Vulnerabilities S3 have –
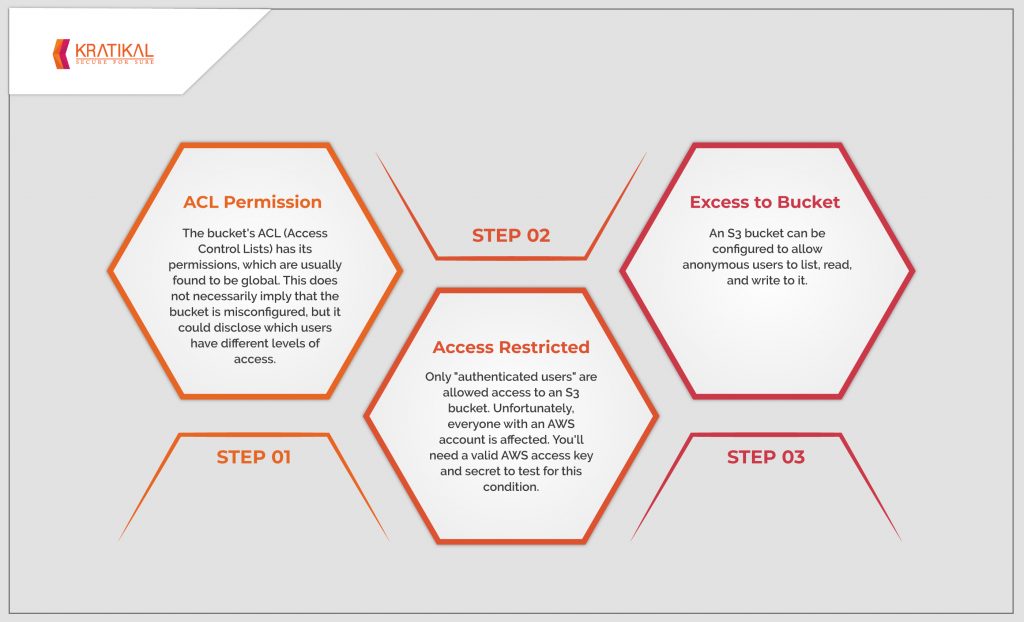
- ACL Permission – The bucket’s ACL (Access Control Lists) has its permissions, which are usually found to be global. This does not necessarily imply that the bucket misconfigured, but it could disclose which users have different levels of access.
- Access Restricted– Only “authenticated users” allowed access to an S3 bucket. Unfortunately, everyone with an AWS account affected. You’ll need a valid AWS access key and secret to test for this condition.
- Excess to Bucket – An S3 bucket can configured to allow anonymous users to list, read, and write to it.
How One Can Protect S3 data from Cyber-Attacks?
- Monitoring: – Your security and compliance teams will need to know who has access to your S3 buckets and what actions they’re attempting, and a secure architecture will be able to block potentially destructive or malicious behaviors.
- Accessible: – Even though AWS’s policies let you determine who has access to which buckets and even support SSO, you should consider the few requirements for more comprehensive security like Centralized access control for your team’s S3 and users of your data can get authentication and access based on their SSO group membership.
- Audit: – It’s crucial that sensitive data stored in S3 can audited. Customers, regulators, and other stakeholders require precise reports on how data protected in S3 and every repository your firm controls, as well as audit logs disclosing who has accessed the data entrusted to you. This involves logging not only data operations, but also all changes to your data-protection policies, for best-in-class security.
What role does VAPT Play?
AWS cloud services must be set up to ensure that security best practices followed. Because many organizations are unfamiliar with some of these best practices, we use VAPT services to scan the configuration and establish testing, covering important services to discover any misconfigurations or vulnerabilities.
This strategy could help you find and fix any existing code problems before they’re exploited by hackers.
Because hackers’ tools, strategies, and procedures for breaching networks are always improving, it’s critical to assess your organization’s cyber security frequently.
With time, Vulnerability and Penetration Testing (VAPT) will become more important for your firm. Following the methods mentioned above, you can do it yourself. You can also turn to kratikal for professional help.
If you have any additional questions about VAPT, please contact us by leaving a comment in the box below and we will be pleased to assist you!







Leave a comment
Your email address will not be published. Required fields are marked *