How safe is your data? With the increasing reliance on online services, this question weighs heavily on everyone’s mind. The recent cyber incident serves as a wake-up call, exposing a vulnerability we often overlook: the security of APIs.
A recent data breach at a well-renowned American technology company affected 49 million consumers and highlights an important concern in today’s digital landscape: API security. This incident serves as an evident example that organizations must prioritize strong Application Programming Interface security measures to secure sensitive data and avoid cyberattacks.
Table of Contents
What Happened?
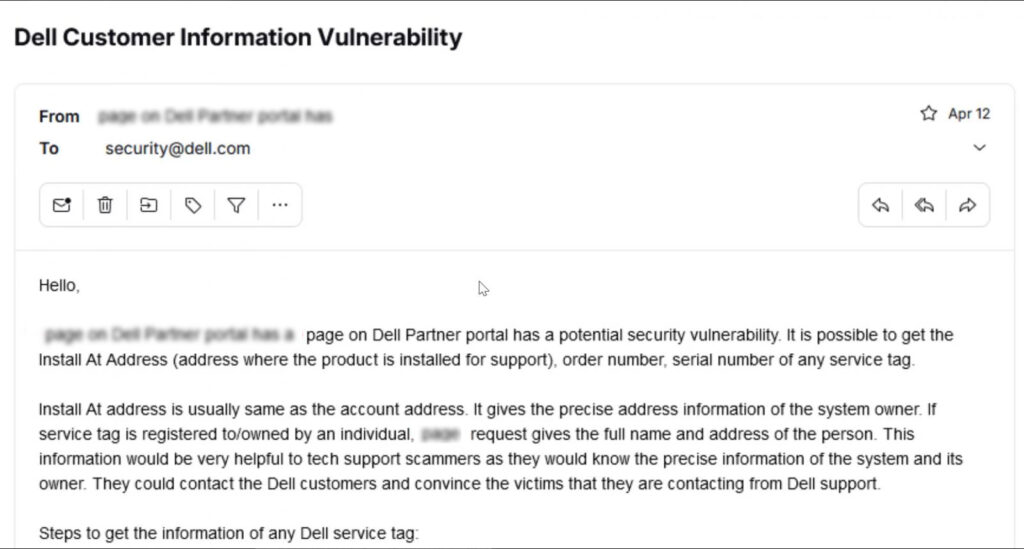
The Dell’s data breach exploited a flaw in an API (Application Programming Interface), a software intermediary that allows apps to communicate with one another. Hackers exploited this vulnerability to get unauthorized access to a large amount of consumer data.
Dell reports that the threat actor obtained the following information during the breach:
- Name
- Physical Address
- Dell hardware and order information, including service tag, item description, date of order, and related warranty information
The stolen client records have the following hardware breakdown:
- Monitors: 22,406,133
- Alienware Notebooks: 447,315
- Chromebooks: 198,713
- Inspiron Notebooks: 11,257,567
- Inspiron Desktops: 1,731,767
- Latitude Laptops: 4,130,510
- Optiplex: 5,177,626
- Poweredge: 783,575
- Precision Desktops: 798,018
- Precision Notebooks: 486,244
- Vostro Notebooks: 148,087
- Vostro Desktops: 37,427
- Xps Notebooks: 1,045,302
- XPS/Alienware desktops: 399,695
Why is API Security Important?
APIs are the basis of modern apps, integrating several services and effortlessly transferring data. However, these portals might become security vulnerabilities if not properly safeguarded.
Here’s why securing APIs is important:
Increased Attack Surface: APIs significantly broaden an organization’s attack surface, providing additional access opportunities for hackers.
Data Exposure: APIs frequently handle sensitive client information, financial details, and internal operations. A breach may disclose this information to unauthorized persons.
Lack of Awareness in the Organization: API security is often an afterthought compared to traditional network security, leaving organizations unprepared for API-based attacks.
Consequences of an API Breach
The potential consequences of an API security breach are beyond just the data exposure.
It could lead to:
Financial Loss: Companies may face hefty fines from regulatory bodies and incur costs associated with customer notification and remediation.
Reputational Damage: A data breach can significantly damage an organization’s reputation, leading to lost customer trust and brand loyalty.
Operational Disruption: A severe API breach can disrupt core business operations, hindering productivity and revenue generation.
Book Your Free Cybersecurity Consultation Today!
API Security Measures
These API security measures could have helped prevent this cyber attack:
API Gateways: These act as central hubs for managing and securing API traffic, offering functionalities like authentication, authorization, and throttling.
Encryption: Encrypting data at rest and in transit helps protect sensitive information even if it’s intercepted by attackers.
Regular Updates: Keeping APIs and underlying systems updated with the latest security patches is crucial to address newly discovered vulnerabilities.
Actionable Steps to Prevent a Data Breach
Transparency is Key: Downplaying the severity of a breach undermines trust with the media, customers, and regulators. Open communication and responsibility are critical during a data breach.
Multi-Factor Authentication (MFA) is a Must: While not foolproof, MFA significantly reduces the risk of account takeover by adding an extra layer of verification during login.
Zero Trust: As a proactive approach, implementing a zero-trust security model would have further restricted access. Even with valid credentials, the hacker would have needed additional verification to reach sensitive data.
Consider Consultation from Cybersecurity Company: Implement the expertise of security experts to assess your API security posture, identify vulnerabilities, and recommend robust solutions.
By adopting these actionable steps, organizations can build stronger defenses and minimize the impact of potential future breaches.
Get in!
Join our weekly newsletter and stay updated
Kratikal: Industry Experts’ Opinion
Kratikal’s team of experts emphasizes proactive measures like regular API security testing and penetration testing (VAPT) to identify vulnerabilities before attackers exploit them. They highlight the importance of “shifting left” in security by integrating security measures throughout development and enabling a strong security culture in organizations to report suspicious activity. The practice of shifting left’ in security emphasizes incorporating security measures throughout the software development lifecycle. This implies including security testing into the development process as early as possible, rather than as an afterthought.
Key Takeaway
The recent data breach incident is an alert for businesses. One must prioritize API security to protect their data and prevent cyberattacks. Kratikal, a CERT-In empanelled company that has been in this field for over 12+ years and has served 450+ SMEs and enterprises, can assist you in securing your API.
Companies may maintain the security of their APIs by establishing rigorous security mechanisms and conducting frequent testing. This can prevent the next potential breach from compromising millions of customers’ data.
Ref: https://www.bleepingcomputer.com/news/security/dell-api-abused-to-steal-49-million-customer-records-in-data-breach/
FAQ
- What happened in the Dell data breach?
Hackers exploited a vulnerability in an API (an intermediary that allows apps to communicate) to access information on 49 million Dell customers. This included names, addresses, and details about Dell hardware purchases. - What is API Security testing?
API security testing is the process of scanning APIs for vulnerabilities that could be exploited by attackers. It involves simulating real-world attacks to find flaws in authentication, authorization, data validation, and other security controls. - Why is API security important for businesses?
APIs often handle confidential customer data like financial details or internal operations. A breach can expose this data to unauthorized users. By securing APIs, businesses reduce their overall attack surface and make it tough for attackers to gain access to critical systems.








Leave a comment
Your email address will not be published. Required fields are marked *