We talk about ‘Vulnerability Management’ collectively as important! But, when security is not confined to only “finding every CVE” and more about shrinking exploitable paths faster than the business ships change, we need to go inclusive and focus on everything. Today, we focus on ‘managing cloud vulnerability’. Security leaders can’t buy their way out of volume; they have to buy better prioritization, better validation, better remediation plumbing, and, for that, a good cloud scanner. We bring to you 7 cloud vulnerability scanners that matter in 2026 for ‘security of your organization’.
Table of Contents
Why Cloud Scanner? What are the Numbers?
- As of the current National Vulnerability Database totals, the public CVE room includes hundreds of thousands, and it keeps climbing.
- In the Verizon 2025 DBIR executive summary, exploitation of vulnerabilities as an initial access vector reached 20%, with edge devices/VPNs at 22%; and even where organizations “worked very hard,” only ~54% of edge device vulnerabilities were fully remediated, with a median of 32 days to remediate.
That’s the operational gap your cloud vulnerability scanners have to close. If it doesn’t, you need to read further!
7 Cloud Scanner for Vulnerabilities in 2026
- AutoSecT by Kratikal
- Wiz
- Sysdig
- Prisma Cloud
- Microsoft Defender
- Orca Security
- Tenable
Thinking Which Cloud Vulnerability Scanner To Have?
Let’s ease up the search. Understand, your board doesn’t care that you found 200,000 issues. They care that you reduced the probability of a material incident. The fastest route is a cloud scanner that
- builds a real inventory
- prioritizes by exploitability and exposure,
- integrates into engineering workflows, and
- proves improvement over time.
Top 7 Cloud Scanners in 2026
Evaluated through a leadership lens like coverage, validation, runtime visibility, DevSecOps integration, and commercial fit, here’s everything you need to know –
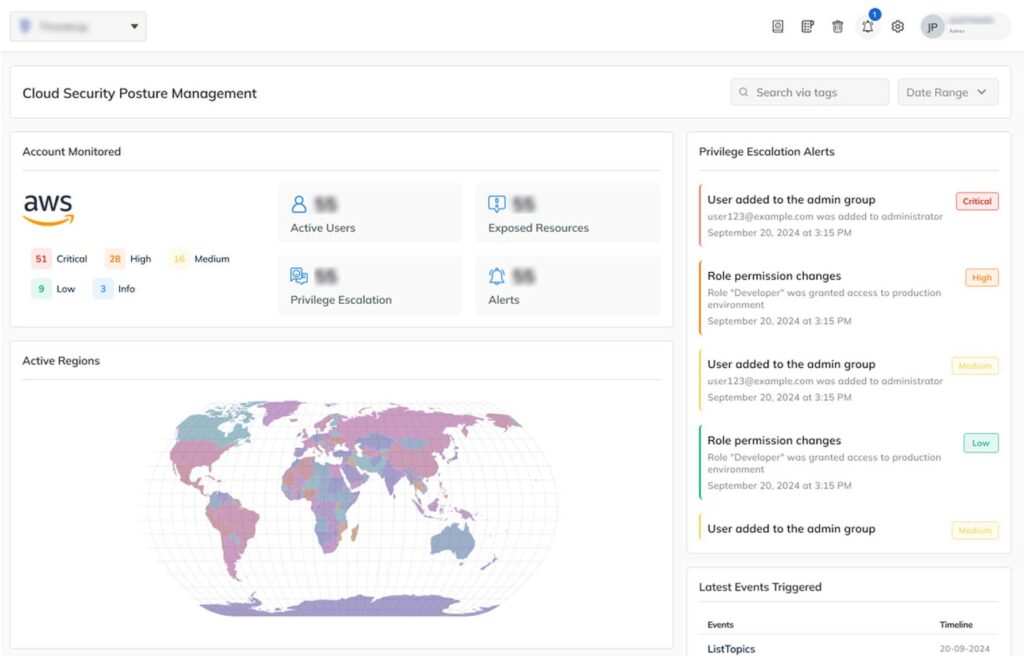
AutoSecT by Kratikal
AutoSecT is an AI-powered VMDR and pentest platform and a cloud vulnerability scanner that specializes in CSPM (Cloud Security Posture Management), Vulnerability Exposure Management, Agentless Asset & Vulnerability Discovery, Real-Time Cloud Monitoring as well as AI-driven Reconnaissance. Instead of heaping your organization with multiple cloud security solutions, AutoSecT guarantees your cloud security and cloud-native inventory security with limited yet highly effective results. To date, it has proven to keep its place in the front row of the ‘greatroom’ termed ‘near-zero false positives’.
Core Capabilities of AutoSecT Cloud Scanner:
CSPM:
AutoSecT’s CSPM continuously evaluates cloud configurations against best practices and compliance benchmarks. It identifies misconfigurations, excessive permissions, and risky exposures early, helping security teams correct structural weaknesses before they become exploitable entry points.
Vulnerability Exposure Management:
Rather than listing thousands of vulnerabilities, this module focuses on contextual risk. It correlates asset criticality, exploit availability, and exposure paths to prioritize remediation, enabling teams to fix high-impact weaknesses and not chase low-risk findings.
Container/Host/Cloud Workload Scanning:
Using agentless discovery methods, the platform scans VMs, containers, and serverless workloads without deployment overhead. It leverages cloud APIs and metadata analysis to maintain visibility across dynamic environments, ensuring transient assets are assessed before they disappear.
Real-Time Cloud Monitoring:
Continuous monitoring in run time detects configuration drift, IAM changes, public exposures, and anomalous behavior as they occur. This reduces detection lag and allows teams to respond to cloud missteps or suspicious activities before they evolve into material security incidents.
AI-driven Reconnaissance:
The AI-driven reconnaissance engine analyzes patterns across assets and exposures to uncover attack paths that traditional scans often miss. By reducing noise and highlighting realistic exploitation scenarios, it enables more informed, risk-based security decision-making.
CI/CD Integration:
Seamlessly integrates with Jenkins and popular ticketing/collaboration platforms, including bi-directional JIRA sync, Google Chat, Slack, Microsoft Teams, and Zoho Cliq, ensuring streamlined workflows and faster remediation cycles.
Cloud Platform Support:
AutoSecT scans AWS, Azure, and Google Cloud environments via agentless approaches and its cloud config audit offering.
Vulnerability Compliance Mapping:
Correlates vulnerabilities with leading compliance frameworks like ISO 27001, SOC 2, and NIST, helping you stay aligned with industry standards and regulatory mandates while prioritizing remediation with AI-driven recommendations and context.
Book Your Free Cybersecurity Consultation Today!
Wiz
Wiz is a Cloud Native Application Protection Platform (CNAPP) that provides broad cloud risk visualization and continuous scanning across multi-cloud environments. It combines agentless discovery with optional runtime visibility to help teams identify security issues in their infrastructure, workloads, and configurations.
Core Capabilities of Wiz
- VM/Container/Serverless Scanning
- Runtime Security
- Detection Signals & Risk Context
- CI/CD Integration
- Multi-Cloud Support
Sysdig
Sysdig provides a cloud-native security platform designed to help teams secure their cloud infrastructure, containers, and workloads with an emphasis on runtime insights and prioritized risk visibility. It combines multiple security functions, such as vulnerability management, cloud posture management, and detection and response, into a unified offering.
Core Capabilities of Sysdig
- Vulnerability Scanning & Management
- Runtime Security & Threat Detection
- Cloud Posture & Misconfiguration Checks
- Cloud Attack Graph
- Multi-Cloud Support
Prisma Cloud
Prisma Cloud is a comprehensive cloud scanner that provides visibility and protection across cloud infrastructure, workloads, networks, and identities. It aims to help organizations manage cloud risks through a combination of cloud posture management, workload security, vulnerability scanning, compliance monitoring, and threat detection, integrated into a broad security suite.
Core Capabilities of Prisma Cloud
- Cloud Posture Management (CSPM)
- Vulnerability Management
- Runtime Protection & Threat Detection
- CI/CD and DevSecOps Integrations
- Multi-Cloud Support
Microsoft Defender
Microsoft Defender for Cloud is a cloud-native application protection platform offered by Microsoft that helps organizations strengthen their cloud security posture across hybrid and multicloud environments. It combines continuous posture assessment, vulnerability scanning, compliance checks, and contextual risk insights into a unified security experience that spans development through runtime.
Core Capabilities of Microsoft Defender
- Cloud Security Posture Management (CSPM)
- Vulnerability Scanning
- Contextual Risk Insights & Attack Path Analysis
- Compliance and Governance Monitoring
- Multi-Cloud and Hybrid Support
Orca Security
Orca Security is a cloud security platform focused on helping organizations secure their multi-cloud environments by providing broad visibility, contextual risk insights, and unified risk prioritization across cloud assets and workloads. Its agentless-first approach and patented SideScanning™ technology enable security teams to assess risks throughout the cloud stack without deploying agents on every asset.
Core Capabilities of Orca Security
- Cloud Posture & Misconfiguration Management
- Contextual Risk Prioritization
- Workload & Cloud Security
- CI/CD & Lifecycle Integration
- Multi-Cloud Coverage
Tenable
Tenable Cloud Security is a cloud vulnerability scanner designed to help organizations gain broad visibility and context into their multi-cloud environments by exposing, prioritizing, and remediating cloud misconfigurations, vulnerabilities, identity risks, and data exposures. It integrates posture management, vulnerability assessment, identity entitlements, and compliance capabilities within a unified cloud security solution.
Core Capabilities of Tenable
- Cloud Posture & Misconfiguration Assessment
- Vulnerability Exposure & Prioritization
- Identity-Driven Risk Insights
- Contextual Cloud Exposure Mapping
- Multi-Cloud & Lifecycle Support
Get in!
Join our weekly newsletter and stay updated
Cloud Scanner – All 7 Comparison Table
| Cloud Vulnerability Scanner | Runtime Security | Cloud Support | USPs |
| AutoSecT | Real-time Monitoring | AWS/Azure/GCP | Near zero false positives |
| Wiz | Mostly agentless-first messaging | AWS/Azure/GCP | Highest ‘Current Offering’ Score |
| Sysdig | Strong | AWS/Azure/Google Cloud + on-prem | Leading in CNAPP Q1 2026 |
| Prisma Cloud | Yes | AWS/Azure/GCP/OCI/Alibaba/IBM | 3,000+ built-in policies |
| Microsoft Defender | Yes | AWS/Azure/GCP | 50% fewer false positives |
| Orca Security | Orca Sensor | AWS/Azure/GCP | 20+ vulnerability data sources |
| Tenable | Yes | Multi-Cloud | Strong Performer – CNAPP Wave Q1 2026 |
Cloud Scanner FAQs
- What do a good cloud scanner detect?
Cloud scanners detect misconfigurations like publicly exposed buckets, excessive IAM permissions, and open ports that increase risk. They also identify known CVEs, along with compliance gaps against CIS benchmarks and regulatory requirements.
- What is the best cloud vulnerability scanner in 2026?
If you need one blunt answer: the “best” is the one that measurably reduces exploitable risk in your environment fastest, not the one with the longest feature checklist. We recommend AutoSecT along with the other top 6 cloud scanners mentioned in the blog.
- How to do a cloud vulnerability scan?
To perform a cloud vulnerability scan, define the scope, integrate a cloud scanner with least-privilege access, and enable checks for CVEs, misconfigurations, and compliance gaps.
- What is a cloud scanner?
A cloud vulnerability scanner is a security tool that continuously analyzes cloud environments to identify misconfigurations, vulnerabilities, exposed assets, and compliance gaps.









Leave a comment
Your email address will not be published. Required fields are marked *