Our digital world is based on connectivity, but with that comes great responsibility. Businesses manage vast amounts of client information. Ensuring the protection of this information is not an easy task, especially given the company’s present obligations. This is why SOC 2 Compliance Audit is essential. It is important to rebuild trust and strengthen cybersecurity in this interconnected world.
In this blog, we will look at the fundamentals of SOC 2 compliance, including trust service requirements, types of reports, and much more. In addition, we will cover the necessity of SOC 2 audits for businesses, concluding with how Kratikal may assist you in becoming SOC 2 compliant.
Table of Contents
What is SOC 2 Compliance?
SOC 2 stands for System and Organization Controls 2. It’s not a certification, but rather an auditing procedure developed by the American Institute of CPAs (AICPA). SOC 2 provides a framework for assessing an organization’s controls for security, availability, processing integrity, confidentiality, and privacy. Let’s take a look at each aspect in detail:
5 Key Trust Service Criteria of SOC 2 Audit
A SOC 2 audit assesses how effectively a service organization manages customer data based on five key Trust Service Criteria:
Security: This focuses on protecting systems and data from unauthorized access, ensuring their confidentiality and integrity.
Availability: This ensures customer data and systems are accessible when needed, minimizing downtime and disruptions.
Processing Integrity: This verifies that data processing is accurate, complete, and reliable, preventing errors or unauthorized modifications.
Confidentiality: This ensures that only authorized individuals have access to confidential customer information.
Privacy: This assesses the organization’s commitment to data privacy regulations and its practices for collecting, using, retaining, and disposing of customer data.
Get in!
Join our weekly newsletter and stay updated
Types of SOC 2 Audits
SOC 2 Type 1 Audit
A SOC 2 Type 1 audit serves as a detailed blueprint. It analyzes the design of an organization’s security controls at a given point in time. An independent auditor determines if these controls meet the five core SOC 2 Trust Service Criteria, which include security, availability, processing integrity, confidentiality, and privacy. This audit provides an important snapshot, indicating a commitment to strong security design. However, it does not evaluate how well those controls are implemented in practice.
Benefits of Type 1 Audit
- Faster and more cost-effective compared to a Type 2 audit.
- Provides a baseline assessment of security controls.
- Demonstrates a commitment to security design to potential customers.
Limitations of Type 1 Audit
- Doesn’t assess the effectiveness of controls over time.
- Doesn’t ensure that controls are being followed regularly.

SOC 2 Type 2 Audit
A SOC 2 Type 2 audit is the preferred method for a more thorough review. It goes beyond the planning stage, functioning as the main part of SOC 2 audit after SOC 2 Type 1 audit. Here, the auditor carefully assesses the operational efficiency of the controls. They evaluate not just the required controls, but also evaluate how consistently they are implemented. Furthermore, they take a look at how the organization monitors and manages them, and how they handle security problems. This comprehensive assessment provides the highest level of trust and assurance about data security.
Benefits of Type 2 Audit
- Provides the most comprehensive assurance of data security.
- Demonstrates that controls are not just designed well, but also work effectively in practice.
- Offers the highest level of trust for potential customers.
Limitations of Type 2 Audit
- More time-consuming and expensive compared to a Type 1 audit.
- Requires a longer time for preparation and documentation.
Key Parties Involved in SOC 2 Compliance
To start with, the lead implementer, who is frequently an internal employee, is in charge of developing and implementing compliance initiatives. They manage the deployment of security procedures, coordinate internal teams, and assure compliance with SOC 2 standards.
Second, external auditors, usually certified SOC 2 auditors, conduct independent audits of the organization’s controls and practices. Their responsibilities include evaluating the effectiveness of implemented procedures, examining documentation, and ensuring requirements of compliance by being SOC 2 Compliant.
Furthermore, stakeholders such as IT professionals, security specialists, and legal advisers offer their knowledge of various parts of SOC 2 compliance. Their insights help in the design and implementation of appropriate controls, bridging gaps, and ensuring compliance.
Collaboration among these parties is essential for successful SOC 2 compliance. It is because this ensures a comprehensive approach to data protection and risk management. Hence, this increases the trust and confidence in the organization’s security procedures.
Why is SOC 2 Audit Important for Businesses?
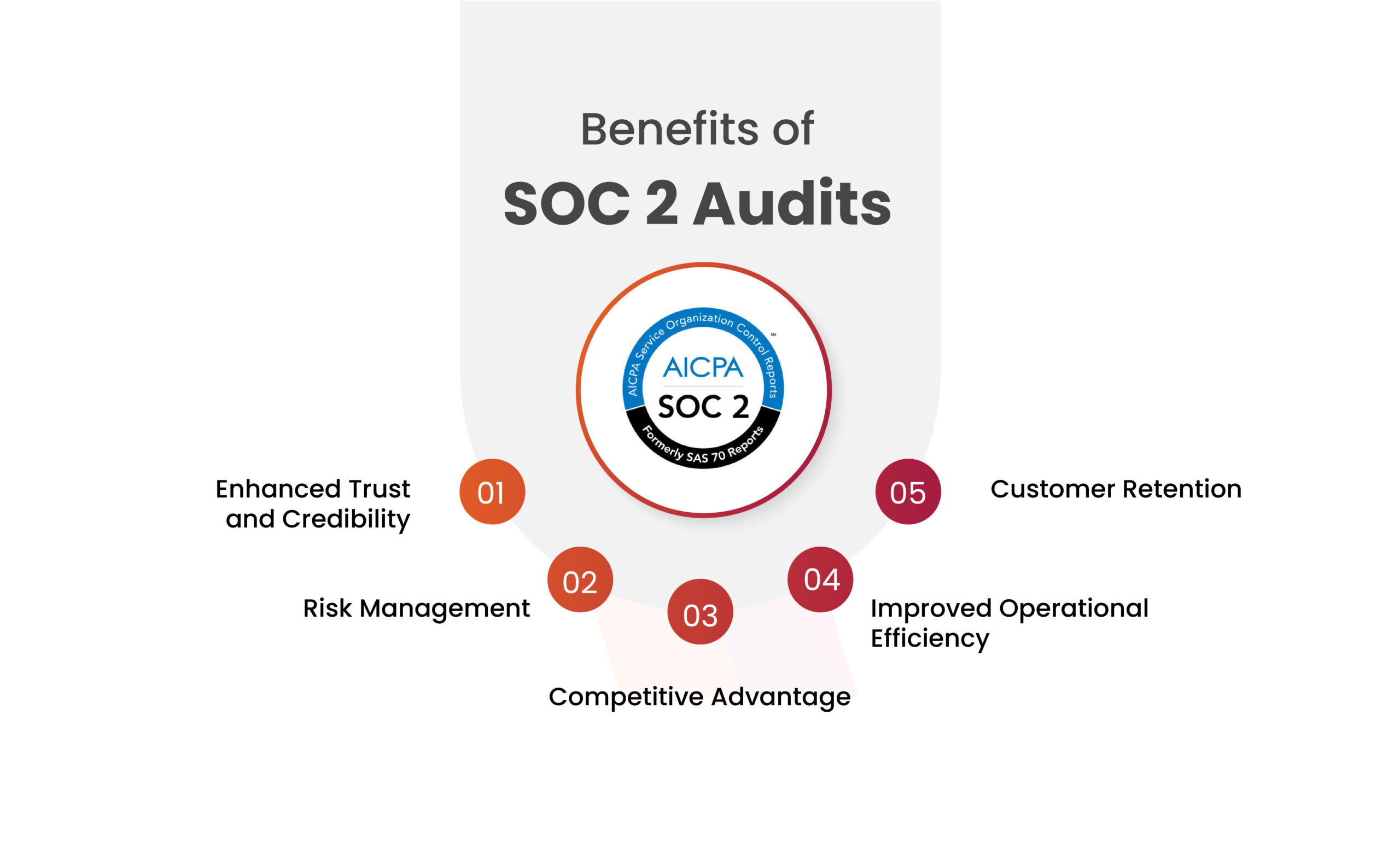
The SOC 2 audit has evolved as an important certification for building trust and transparency for several service provider businesses. This formal attestation procedure certifies a service organization’s adherence to high security standards, particularly those governing customer data protection. SOC 2 audits highlight service providers’ commitment to strong information security standards. This not only builds trust with potential and existing clients, but it also improves internal controls and risk management, resulting in a more secure and robust business environment.
Approach to SOC 2 Compliance
Using a structured approach to a SOC 2 compliance audit allows service providers to demonstrate their commitment to strong information security standards, establishing confidence with potential and existing clients.
Here’s a breakdown of a formal approach to a SOC 2 compliance audit:
Selection of Audit Type: The first step is determining the appropriate SOC 2 audit type. A Type 1 audit focuses on the design of your security measures at a certain point in time, but a Type 2 audit goes deeper into security measures and evaluates the operational efficacy of those controls over a specific time. Consider your organization’s security maturity, customer requirements, and resource limits while making this selection.
Gap Analysis and Control Selection: Conduct a thorough gap analysis to identify any discrepancies between your existing controls and the 5 SOC 2 Trust Service Criteria. Based on this analysis, select the relevant controls you’ll implement to address these gaps.
Policy and Procedure Development: Develop or update your existing security policies and procedures to document the chosen controls. These policies should clearly outline how the controls will be implemented, monitored, and maintained.
Implementation and Testing: Implement the chosen security controls across your organization. Following implementation, conducting pentesting (VAPT) to ensure their effectiveness in achieving the desired security objectives.
Documentation and Evidence Collection: Meticulously document your security controls, policies, and procedures. Gather comprehensive evidence demonstrating the implementation and ongoing effectiveness of these controls.
Selection of a SOC 2 Auditor: Engage a qualified and independent SOC 2 auditor. The auditor will assess your controls, documentation, and evidence to determine your adherence to the SOC 2 Trust Service Criteria.
Audit Process and Reporting: Work collaboratively with the auditor throughout the examination process. Following the audit, you’ll receive a SOC 2 report that details the auditor’s findings and their opinion on your compliance with the chosen Trust Service Criteria.
Book Your Free Cybersecurity Consultation Today!
How to Achieve SOC 2 Compliance?
To achieve SOC 2 Compliance,
- Develop and implement internal controls that address each TSC principle. These controls can be technical (firewalls, encryption) or procedural (background checks, access controls).
- Document your controls clearly and comprehensively.
- Get your controls audited by a licensed SOC 2 auditor. The auditor will assess how well your controls meet the TSC and issue a SOC 2 report. There are two main types of reports:
SOC 2 Type 1: The report provides a review of the design and operational effectiveness of the controls over 3-12 months.
SOC 2 Type 2: The report goes beyond design and assesses the effectiveness of your controls and a broader range of data management over a period of time.
Service Organization Control 2 compliance is an ongoing process. You’ll need to continuously monitor and update your controls to maintain compliance.
Conclusion
With over 12 years of expertise and being a CERT-In empanelled auditor, Kratikal is a reliable partner in improving safety and compliance. We provide a reliable approach to strengthen organizational security and assure adherence to SOC 2 compliance audits. Businesses with the help of Kratikal’s team of experts navigate the complexity of SOC 2 compliance, from selecting the proper SOC 2 audit type to establishing strong security measures. With Kratikal’s assistance, organizations may not only demonstrate their commitment to protecting client information, but also establish trust, manage risks, and build a resilient cybersecurity posture.
FAQ
- Why is SOC 2 Audit important for Organizations?
SOC 2 compliance is essential for organizations because it displays their commitment to protecting consumer data and maintaining strict security requirements.
- What are the key differences between SOC 2 Type 1 and Type 2 audits?
SOC 2 Type 1 audits assess an organization’s control environment, focusing on design and implementation. Type 2 audits offer a more comprehensive evaluation over time, assessing effectiveness and consistency.









Leave a comment
Your email address will not be published. Required fields are marked *