
Government agencies were in a state of shock when they realized that their systems have been compromised with the malicious TeamViewer software. The attacker who was responsible for this attack is a Russian speaking man. TeamViewer is one of the most popular tools for the remote access of desktop, desktop sharing, file transfer between systems, web conferencing etc. The motive behind the attack is probably financially driven. The software was manipulated by adding malicious TeamViewer DLL to the original software. This mala fide software can steal sensitive data and money from even government and financial networks.
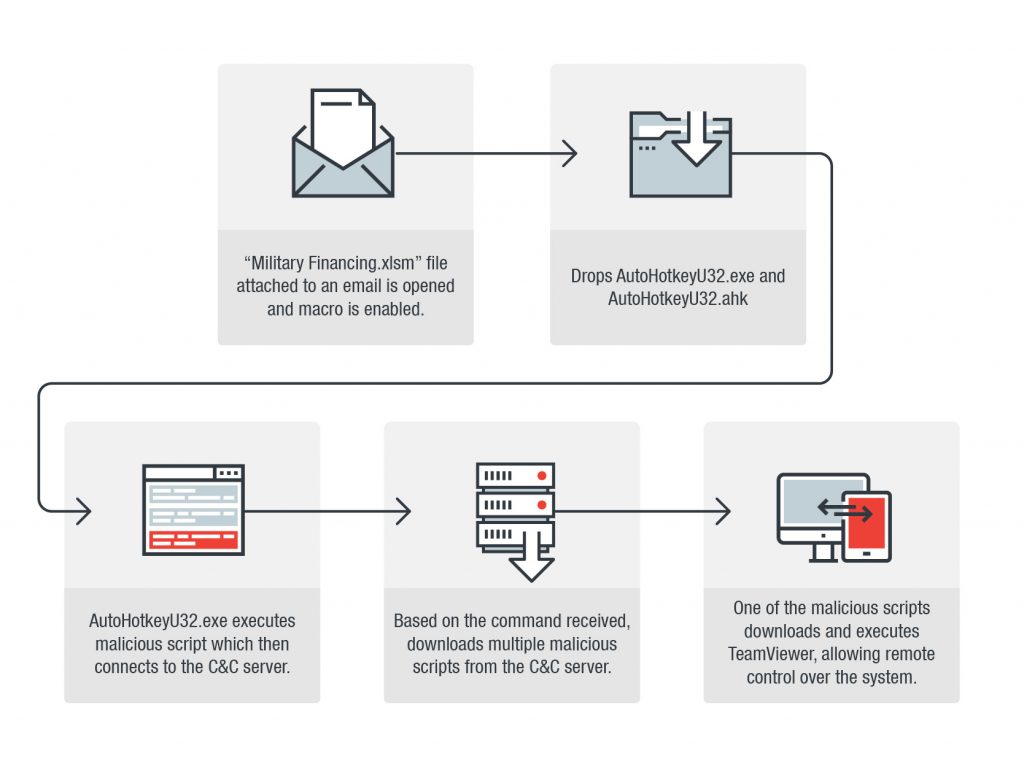
A malicious email posing to be sent from the U.S. Department of State was delivered in the inbox of the government employees and had ‘Military Financing Program’ as its subject line. The email had a malicious XLSM attachment with embedded macro.
Employees were duped by the malicious email since the emails coming from the U.S. department of state are generally marked as top secret. Once the victim opened and enabled macro in the decoy document, two files were extracted from the hex encoded cells in the XLSM document. The first one was the genuine AutoHotkeyU32.exe program. The other one was the corrupted AutoHotkeyU32.ahk which is an AHK script used to communicate with C&C server and to download the additional script and execute it.
How did the attacker successfully deploy the attack?
There are three different kind of malicious AHK scripts including ‘hscreen.ahk’, ‘info.ahk’ and ‘htv.ahk’. These three scripts affect user’s system in different ways.
hscreen.ahk: This script takes the screenshot of the victim’s personal computer and upload it on the C&C server.
hinfo.ahk: Victim’s username and computer information is sent to the C&C server.
htv.ahk: A malicious version of TeamViewer is downloaded, executed on victim’s system and login credentials are sent to the C&C server.
The attacker hid the genuine TeamViewer interface while the TeamViewer software with malicious ‘htv.ahk’ was being run. DLL in order to take over the control of the software. This allowed the attacker to replace the genuine TeamViewer with the manipulated version.
The attack targeted Public financial sector and government officials belonging to Kenya, Italy, Liberia, Bermuda, Guyana, Lebanon and Nepal.
Earlier in the month of January, a security researcher who goes by the name of FewAtoms found a URL containing a malicious self-extracting archive which is a spyware disguised as TeamViewer.
The researchers have found a link of an avatar connected to a Russian underground forum user known as EvaPiks.
What could have been done?
- Ensure that the AHK script is compiled with ahk2exe, which is the part of AHK distribution.
- In order to prevent de-compilation, provide a good password.
- Always check the extension of any attachments present within the email.
- Organizations should implement a multi-layer defense and put mitigation protocols in place to detect intrusions and act against them.
- Enhance settings for macro malware attached emails.
- Ensuring the application of these methods so that the program runs normally. It will also ensure that attacker would have difficulties in modifying the program.
- However, the most effective strategy is to empower employees against social engineering attacks and provide periodic knowledge imparting sessions.

